I have seen organizations invest millions in cybersecurity solutions only to be compromised by someone who already had legitimate access to their systems. The uncomfortable truth about information security is that your most significant threats are not anonymous hackers launching attacks from distant basements. They are people who pass you in the hallway every day.
After being deeply involved in the cybersecurity industry and leading DekkoSecure for over seven years, I have observed a persistent blind spot in how organizations approach security. While firewalls get fortified and intrusion detection systems grow increasingly sophisticated, the human element remains dangerously under-addressed.
Insider threats should keep security professionals awake at night. Yet they often do not receive the attention they deserve because confronting them means acknowledging an uncomfortable reality: trust is both necessary for business operations and potentially your greatest vulnerability.
The Hidden Face of Insider Threats
When we discuss insider threats, many leaders immediately picture malicious employees deliberately stealing data. While that scenario exists, the reality is far more nuanced. In my experience working with government agencies, law enforcement, and healthcare organizations, insider threats typically fall into three categories, each requiring different mitigation approaches:
Type 1
The malicious insiderThis employee deliberately exfiltrates sensitive information, perhaps to sell it, leverage it for a new position, or satisfy a grudge. These cases make headlines but are not the most common.
Type 2
The negligent insiderThis employee means no harm but takes dangerous shortcuts. They email sensitive documents to a personal account to work from home, share passwords with colleagues, or connect unauthorized devices to secure networks.
Type 3
The compromised insiderSomeone whose legitimate credentials have been stolen or whose account has been taken over. To your systems, their activity appears entirely legitimate despite being unauthorized.
This complexity makes insider threat detection uniquely challenging. A firewall cannot distinguish between legitimate and illegitimate use of proper credentials. Traditional cybersecurity tools struggle to identify when authorized users are doing unauthorized things.
The Escalating Stakes
For the security-conscious organizations we work with at DekkoSecure, including government agencies, law enforcement, healthcare providers, and defense contractors, the stakes could not be higher. An insider breach is not just an inconvenience. It can compromise national security, undermine justice, or expose sensitive personal information.
Real-world example
I consulted with a law enforcement agency that had experienced an insider breach affecting sensitive case files. The compromise did not come from hacking but from an employee with legitimate access who had been copying files to review at home, against policy but without malicious intent. The potential damage to active investigations was substantial.
What makes these situations particularly dangerous is their detection difficulty. External attacks typically leave evidence such as unusual network traffic, failed login attempts, or suspicious IP addresses. Insider threats, particularly from those with proper access, often appear as entirely normal system usage until damage is discovered.
This detection challenge creates what security professionals call "dwell time" — the period between compromise and discovery. The contrast is stark:
Rethinking Security from the Inside Out
Addressing insider threats effectively requires fundamentally rethinking security architecture. Traditional approaches focus on perimeter defense — keeping bad actors out. But when your greatest risks already have legitimate access, you need different strategies.
This realisation drove the development of our approach at DekkoSecure. Working with organizations handling extremely sensitive data, we recognised that truly effective data protection requires minimising trust requirements while maximising usability.
The principle seems straightforward but implementing it is anything but simple. How do you enable secure collaboration on highly sensitive data while minimising the trust placed in any individual user? The answer lies in zero-knowledge systems: architectures where even those administering the systems cannot access the protected data.
Building Trust Through Limited Trust
Creating effective cybersecurity against insider threats involves reconceptualising how we build and deploy systems. Instead of simply trusting authorized users, we need systems that limit what any individual can access, view, or export without proper authorization. This requires four critical capabilities:
Systems must limit access based on multiple factors: not just who someone is, but where they are accessing from, when they are doing it, and what specific parts of the data they truly need. This is the foundation of identity and access management (IAM).
Proper encryption means implementing end-to-end encryption where the keys remain exclusively with authorized users. This ensures that even system administrators cannot access content without proper authorization, not just at transit or at rest.
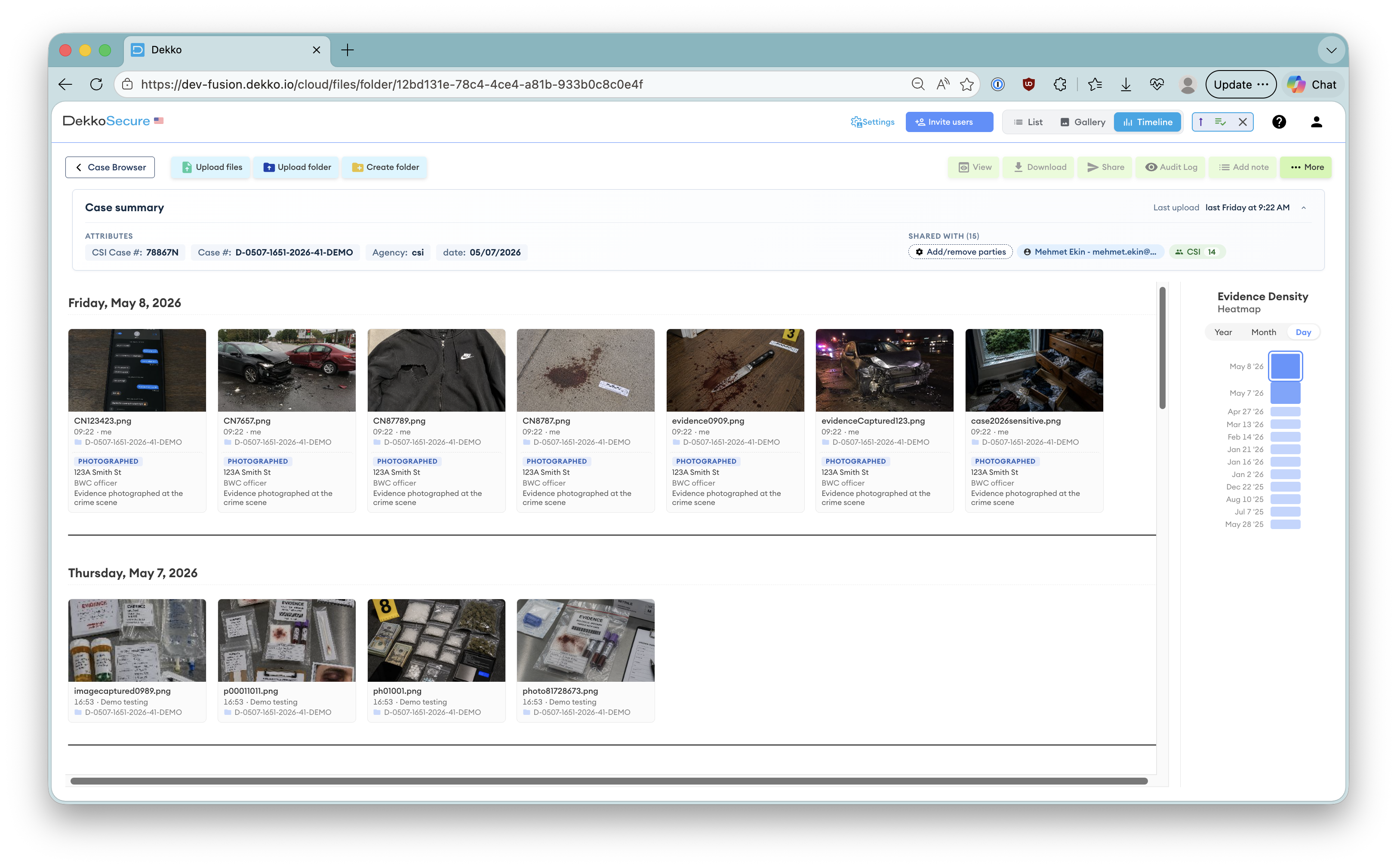
Audit trails must capture not just who accessed what, but what they did with it. When working with law enforcement agencies, we have seen how critical this capability becomes for maintaining chain of custody for digital evidence.
When security measures become too cumbersome, users inevitably find workarounds, creating new vulnerabilities in the process. Security that impedes productivity will never be sustainable.
Making Security Practical
The greatest cybersecurity challenge for most organizations is not technological. It is practical. How do you implement robust protection against insider threats without hamstringing operations?
I have seen too many organizations implement security solutions so onerous that employees develop workarounds, creating even greater vulnerabilities. The art of effective security is finding the balance between protection and productivity. This balance is particularly critical for the organizations we serve at DekkoSecure. Government agencies cannot simply stop sharing information because of security concerns. Healthcare providers need efficient access to patient data. Law enforcement must maintain evidence integrity while enabling investigators to collaborate effectively.
The solution lies in designing security that works with natural human behavior rather than against it. Security must be invisible to be effective.
The Future of Insider Threat Protection
As we look ahead, the challenges of insider threats will only intensify. Remote work has expanded attack surfaces. The value of sensitive data continues to increase. The line between insider and outsider blurs as organizations rely more on contractors, partners, and temporary workers.
Effective protection against insider threats requires a multi-layered security strategy that goes beyond technology alone:
Training that goes beyond compliance checkboxes to create genuine understanding of how insider threats emerge and how individuals contribute to prevention.
Security as everyone's responsibility rather than just IT's problem. Culture determines whether people want to stay within the guardrails that technology provides.
Technology that enables secure collaboration rather than just preventing breaches. When security enhances workflow, adoption follows naturally.
Processes that recognise security as an enabler of mission success rather than an obstacle to it. The framing matters as much as the implementation.
Beyond Technology
Technology can limit what people can access, but it cannot address why some become threats in the first place. Truly comprehensive insider threat programs also consider organizational culture, employee satisfaction, and early identification of potential issues. Technology provides the guardrails, but leadership and culture determine whether people want to stay within them.
The most effective security strategies recognise that insider threats are not just a technical problem. They are a human one. By combining sophisticated technology with thoughtful organizational practices, we can create environments where data security enables rather than restricts essential operations.
The organizations that thrive in this environment will be those that recognise security is not just about keeping bad actors out. It is about ensuring that those you have already let in can only access what they legitimately need.
In a world where your biggest threats already have the password, that balanced approach is not just nice to have. It is essential.
Chief Executive Officer, DekkoSecure
Jacqui Nelson is the CEO of DekkoSecure, an Australian cybersecurity company specializing in zero-knowledge secure file sharing, digital evidence management, and secure collaboration for government, law enforcement, defense, and critical infrastructure sectors.