System Security
DekkoSecure is for agencies and organisations that require confidentiality, integrity, and strict jurisdictional control.
Both DekkoCORE and DekkoDEMS apply the same security foundations to protect sensitive collaboration and digital evidence workflows.
End-to-End Encryption
DekkoSecure uses true end-to-end encryption across all content, including files, messages, signatures, and video meetings. Encryption occurs on the user’s device with AES-256 for symmetric data and ECC-384 for user key pairs. Decryption keys never leave the customer’s control, and encrypted material is never visible to DekkoSecure staff or underlying cloud providers.Zero-Knowledge Security Model
DekkoSecure uses a zero-knowledge architecture that prevents platform staff or cloud providers from viewing customer data in plaintext form. All content remains encrypted during upload, storage, and review, removing insider-access risks and ensuring confidentiality across multi-agency and cross-organisation workflows.
Secure by Design
DekkoSecure is engineered with a Secure by Design philosophy that ensures both DekkoCORE and DekkoDEMS deliver strong, built-in protection without requiring complex configuration. Security controls such as encryption enforcement, MFA, access governance, audit logging, and hardened infrastructure are applied automatically, giving agencies a platform that is secure from first use and resilient throughout collaboration and evidence workflows.Sovereign Hosting and Data Residency
- DekkoCORE is hosted in sovereign environments in Australia, Canada, the United States, and Switzerland, ensuring all encrypted data and metadata remain within the chosen jurisdiction.
- DekkoDEMS is hosted exclusively in the United States to align with justice-sector expectations for evidence handling and disclosure.
Hardened Cloud Infrastructure
DekkoCORE and DekkoDEMS run on a hybrid architecture across Microsoft Azure and Oracle Cloud Infrastructure (OCI), giving the platform a hardened, multi-layered security foundation. Both cloud environments provide advanced physical security, network isolation, continuous monitoring, and robust protections against intrusion.Multi-Tenant Isolation
DekkoSecure uses a secure multi-tenant architecture with per-user and per-file cryptographic separation that prevents unauthorised cross-tenant access. Each organisation’s encrypted data remains isolated from others, and even platform administrators cannot view or decrypt customer content. This design challenges industry norms by combining the benefits of multi-tenancy architecture with E2EE and zero-knowledge protections.Authentication and Identity Controls
DekkoSecure integrates with enterprise and government identity providers through Single Sign-On (SSO), supporting strong authentication controls and conditional access policies. Non-SSO users authenticate using secure TOTP-based MFA. Identity access is enforced consistently across both DekkoCORE and DekkoDEMS, with granular permission structures to support complex, multi-agency workflows.Access Control and Authorisation
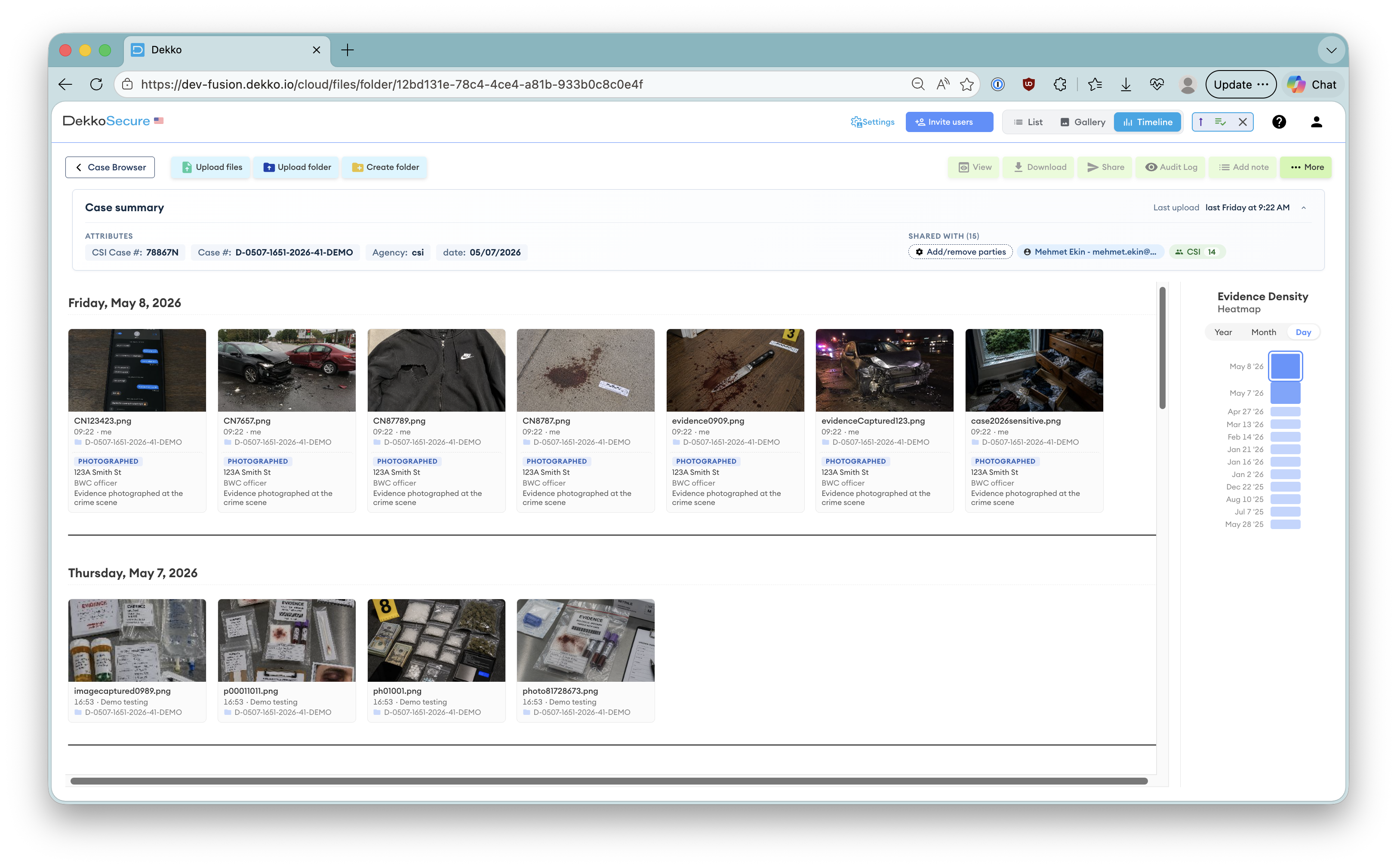
Role-based access controls apply consistently across collaboration spaces, cases, and evidence items. Permissions can be tailored to individuals, groups, or external partners, ensuring users only access the specific content they are authorised to see. DekkoDEMS adds additional controls for case attribution and chain-of-custody workflows.Immutable Audit Logging
DekkoSecure records all collaboration, administrative, and evidence-handling actions in a tamper-evident audit trail. These logs provide comprehensive visibility for investigators, administrators, and prosecutors, supporting chain-of-custody verification, compliance assessments, and defensibility in judicial proceedings.Independent Testing and Assurance
DekkoSecure undergoes regular independent penetration testing and comprehensive security assessments to validate platform resilience. Continuous monitoring, vulnerability management, and secure development practices ensure strong protection against emerging threats across both platforms.
Operational Security and Monitoring
DekkoSecure maintains strict internal security practices, including least-privilege access to operational systems, personnel vetting, and continuous monitoring of infrastructure. Customer environments are isolated with region-specific controls, and no operational staff have access to encrypted content.
Ready to reach out?
If you’d like to learn more about DekkoSecure's compliance status or discuss your requirements, our team is ready to assist.