Security Insights
Why Your "Secure" File Sharing May Be Placing Your Data at Risk
Virtually every week another high-profile breach of sensitive data is reported in the news. Hackers used to be anti-social, shady individuals. Today they are international, sophisticated crime gangs and malicious state actors. The tools they are targeting may already be open on your screen.
Popular "Secure" File Sharing Solutions Are Not Always Safe
"But we're using extremely well-known and popular online secure file sharing solutions," I hear you say. "Our data must be safe because these brands are popular and backed by some of the world's biggest technology companies that heavily promote a high level of data security."
You may want to reconsider after reading this.
Here is a question: do you read the fine print when agreeing to the terms and conditions of the cloud-based file sharing and document collaboration products you, and potentially your whole organization, are using?
The brands are well known. The interfaces are frictionless. But the terms you have agreed to may tell a very different story about what is actually happening to your data.
The Fine Print You May Have Already Agreed To
The following are among the general terms you agree to when using products like the ones listed below:
- The service can read your private emails and content.
- The service retains content that you have chosen to delete.
- Your data may be processed and stored anywhere in the world.
- Voice data is collected and shared with third parties.
- Many third parties are involved in operating the service.
- The service can delete specific content without prior notice and without reason.
Why we do it anyway
We use these platforms because they are easy and the brands are familiar. It is analogous to consuming a heavily promoted product that experts warn carries health risks. Most people know a better option exists but choose convenience instead. When it comes to sensitive data, that tradeoff has real consequences.
True Security Requires Secure-by-Design Solutions
If you truly care about the security of your shared sensitive and confidential data, you need a solution that does not just promote security. One that is built from the ground up with security as priority number one, not as an afterthought.
True security means your shared data is never vulnerable or compromised, and that not even the service provider has access to it. No exonerating fine print. No caveats about third-party access or global data processing. Just protection.
The ASD has published guidance on the importance of choosing products that are secure-by-design, including secure file sharing solutions. The report outlines what to look for and why it matters for organizations handling sensitive information.
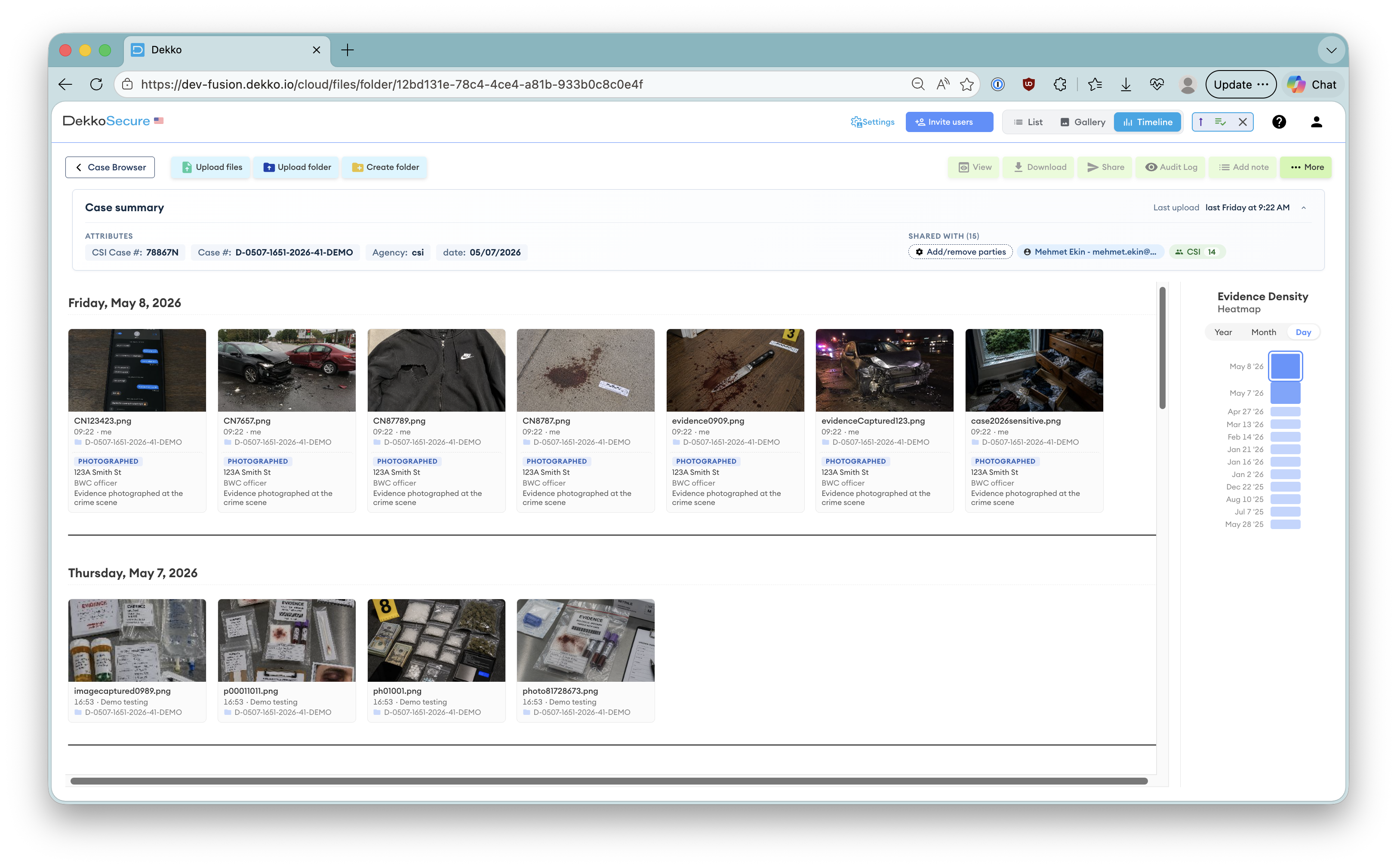
Read the ASD guidance →Highly security-conscious organizations, including law enforcement, government agencies, defense primes, and organizations in the critical infrastructure sector, choose secure-by-design platforms precisely because they cannot afford to rely on fine print instead of architecture.
The question is not whether your current platform promotes security. It is whether the platform's architecture guarantees it.