Data sovereignty has evolved from a background compliance requirement to a front-and-center decision factor in enterprise technology strategy. What was once buried in contract fine print and regulatory checklists has become a determining factor in whether vendors make the shortlist, or get disqualified before the first meeting.
Over the past 18 months, I have watched this shift accelerate across government, law enforcement, healthcare, and defense. The conversation is no longer just about keeping data safe. It is about who controls it, where it lives, and which laws can compel access to it. If you cannot answer those questions with confidence and clarity, you may already be behind.
This is not just a compliance issue anymore. It is a trust issue. And in sectors handling sensitive investigations, classified information, or protected health records, trust is not negotiable.
The Cloud Gave Us Scale. It Also Gave Us Jurisdictional Headaches.
Cloud platforms transformed how organizations operate, delivering flexibility and collaboration capabilities that seemed impossible a decade ago. But they also blurred the lines around where data actually lives and who has legal authority over it. Your data might physically reside in Sydney, but if your provider is headquartered in the US, it could be subject to American law, regardless of geography.
The CLOUD Act challenge
The US CLOUD Act, passed in 2018, allows US law enforcement to demand data from American technology companies even when that data is stored outside US borders. This creates direct tension with regulations like the EU's GDPR, which restricts how and when personal data can move across borders.
For organizations managing digital evidence, sensitive government communications, or defense contractor information, this is a practical risk: can a foreign government potentially access your data through legal processes you cannot control?
Europe has already grappled with these questions. The Privacy Shield agreement between the EU and US was invalidated because the court determined that US surveillance laws could not adequately protect EU citizens' data. Organizations across Europe had to scramble to restructure their cloud arrangements to maintain compliance.
Australia Is Ahead of the Curve, If You Are Paying Attention
Australian government agencies have not waited for a crisis to address sovereignty. If you are selling technology to government, you have encountered IRAP, the Information Security Registered Assessors Program. It is the certification that proves your platform meets PROTECTED-level security controls set by the Australian Cyber Security Centre.
This is not optional. Government agencies, state and federal health departments, law enforcement organizations, and defense suppliers increasingly require IRAP PROTECTED certification as a baseline. Without it, you are not in consideration.
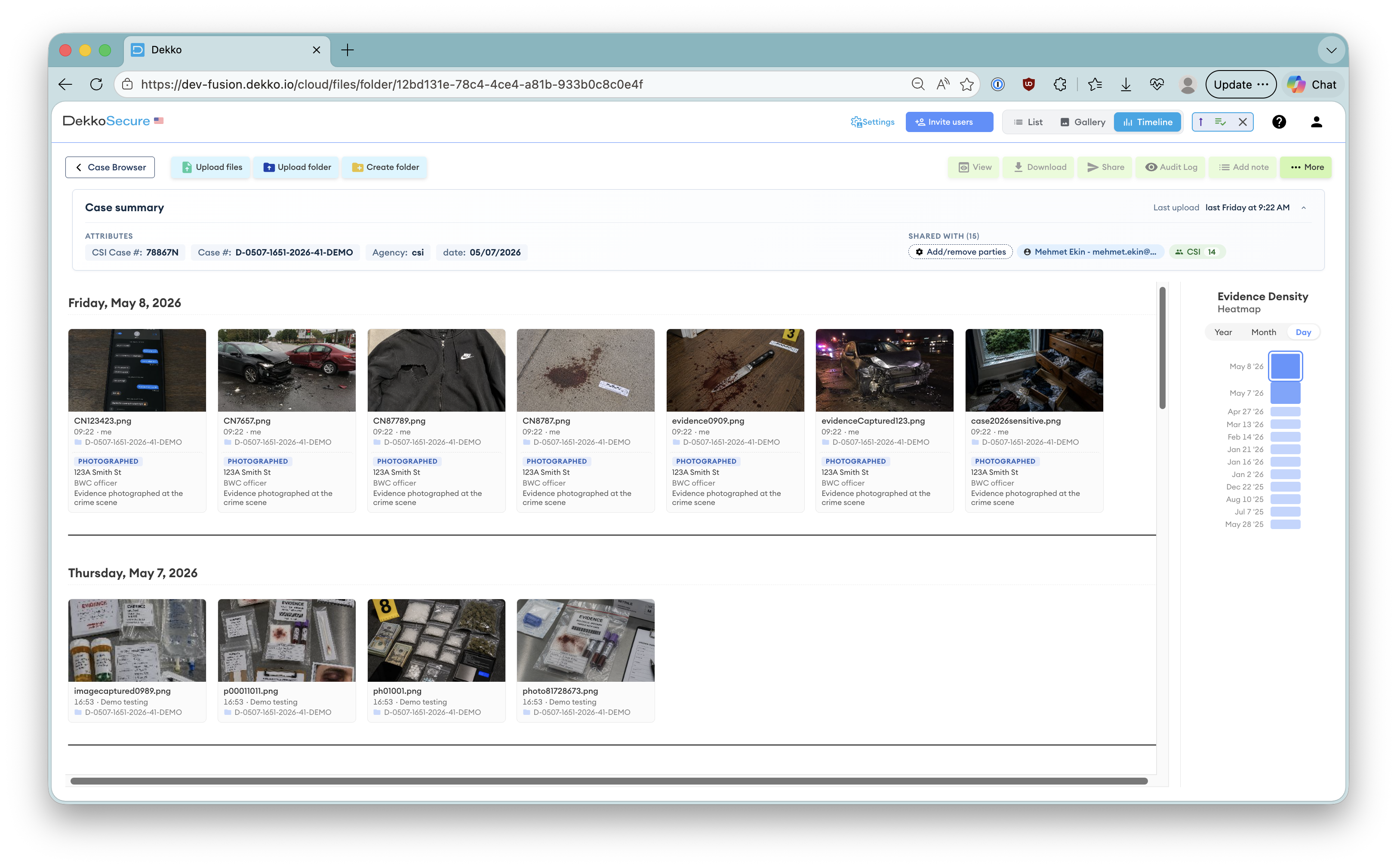
At DekkoSecure, we have completed the IRAP PROTECTED assessment. It is rigorous by design, because it has to be. These controls exist to protect information where exposure could compromise investigations, national security, or public safety. If you are evaluating platforms for digital evidence sharing or secure cross-jurisdictional collaboration, IRAP certification is not a nice-to-have. It is table stakes.
Sovereignty Is Not Just About Location. It Is About Control.
Here is a critical distinction many organizations miss: storing data in Australia does not automatically make it sovereign. If your provider is foreign-owned, manages encryption keys centrally, or operates under unclear access policies, your data is not truly sovereign, even if it never leaves Australian soil.
Real sovereignty requires architectural commitment. At DekkoSecure, we have built this into our foundation:
Your data is encrypted on your device before it reaches the cloud. No backdoors, no workarounds. Even under legal compulsion, we cannot access your files because we do not hold the technical capability to do so.
We cannot share your files, even if someone asks, politely or otherwise. You hold the encryption keys, which means you maintain genuine control over your data at all times.
When someone asks where your sensitive data lives and who can access it, you have clear, defensible answers. Not vague policy statements, but verifiable technical and legal commitments.
This Is About Risk, Not Just Regulation
I work with CISOs and security leaders across law enforcement, defense supply chains, and critical infrastructure who understand this instinctively. Data sovereignty is not about ticking boxes. It is about preventing reputational damage, legal exposure, and operational compromise.
- Defense contractor designs leak overseas through a foreign subpoena issued to a US-headquartered cloud provider.
- A criminal investigation gets challenged because offshore storage created chain of custody questions the prosecution cannot definitively answer.
- A hospital cannot prove patient records stayed within approved jurisdictions, triggering regulatory enforcement and public exposure.
These are not hypothetical scenarios. They are real risks landing on security leaders' desks every week. Smart organizations are moving proactively, prioritizing platforms that combine sovereign hosting, end-to-end encryption, and auditable control.
What You Should Do Now
Know exactly what data you are storing, where it physically resides, and which jurisdictions could legally access it. Do not just think about physical infrastructure — consider jurisdictional reach.
Ask direct questions: Where is data stored? Who owns the platform? Who controls encryption keys? Do you have IRAP PROTECTED certification? Vague answers should raise red flags.
If your platform does not offer zero-knowledge or client-side encryption, ask why. Encrypted in transit is not sufficient for sensitive workloads. Data needs to remain encrypted at rest, with keys you control.
Retrofitting sovereignty into existing systems is expensive, complex, and often incomplete. Platforms built with sovereignty as a foundational principle deliver better security and clearer compliance from day one.
Data sovereignty might show up in compliance frameworks, but at its core it is about maintaining trust with the people who depend on you to protect their information. When citizens share personal information through government portals, court systems, or healthcare providers, they expect protection.
In 2025, that protection extends beyond firewalls and access controls. It includes where data resides, who owns the infrastructure, and whether your platform can legally and technically say no to unauthorized access demands.
When data sovereignty becomes a dealbreaker, your job is to make sure the deal never breaks trust.
Chief Executive Officer, DekkoSecure
Jacqui Nelson is the CEO of DekkoSecure, an Australian cybersecurity company specializing in zero-knowledge secure file sharing, digital evidence management, and secure collaboration for government, law enforcement, defense, and critical infrastructure sectors.