Security Insights
The Easiest Explanation of Confidential Computing You'll Ever Read
In one sentence
Confidential computing keeps your data private from everyone while it is being processed in the cloud, including the cloud provider itself.
To understand why confidential computing matters, you first need to understand the three states of data security, and where the gap used to be.
The Three States of Data
Files stored on servers or drives. Without protection, anyone with access to the storage system could read your files.
Solved by encryption.
Information traveling across networks. Without protection, data could be intercepted as it moves between locations.
Solved by secure transmission protocols.
Information being actively processed, analyzed, or worked on. This is where the gap used to exist, until confidential computing.
Solved by confidential computing.
End-to-end encryption (E2EE) closed part of this gap by shifting processing to the client side. Your local device handles the work, ensuring data never sits unencrypted in someone else's infrastructure. But client-side processing has limits.
When large amounts of data need to be processed, datasets too big for a laptop, real-time collaboration requiring server resources, or multimedia rendering demanding compute power, you need cloud capabilities. That is where confidential computing fills the gap.
Why This Problem Exists
Many organizations cannot use cloud-based tools for sensitive work because processing data in the cloud means trusting the cloud provider with access to it.
Government agencies will not use Microsoft Word Online or Google Docs for classified documents. Healthcare organizations cannot process patient data in traditional cloud environments. Research institutions cannot collaborate on sensitive datasets if it means exposing proprietary information to cloud vendors. The reasons are clear:
- Cloud providers could access your data, intentionally or accidentally
- Data could be subject to legal requests or subpoenas
- Misconfigurations could expose sensitive information
- AI systems could potentially train on your proprietary content
- Sharing controls are inadequate in many systems and can expose data to the wider world
This is the same trust challenge organizations faced with cloud storage a decade ago. We solved that problem with end-to-end encryption and zero-knowledge architectures. Now confidential computing provides the same protection for data processing.
How Confidential Computing Works (The Simple Version)
The basic mechanism is straightforward: encrypted CPU and RAM. When data is being processed, it needs to be in two places.
The mechanism
A hardware-based Trusted Execution Environment, or "secure enclave"
Runs the application code. Confidential computing encrypts this space.
Holds the data being worked on. Confidential computing encrypts this space too.
The result: a hardware-isolated environment where both the code and the data are encrypted, invisible to the cloud provider, the operating system, and any other process on the machine.
The secure data path
It remains encrypted while in transit and until it is inside the protected environment.
Using keys that only the enclave itself can access. Data never sits in an unencrypted state where the cloud provider could read it.
The application code runs on decrypted data within the enclave, returning results that are re-encrypted before leaving.
A mechanism called attestation confirms the enclave is running in secure mode. If protection is disabled, all processing halts automatically to prevent exposure.
The key management
The encryption keys are not accessible to the cloud vendor or even the service provider. They are only accessible to the customer, or they are destroyed entirely. If a key is lost or compromised, a new secure environment is created.
What You Can Do With Confidential Computing
Confidential computing enables use cases that were previously impossible in the cloud:
Multiple agencies can work on sensitive files in real time without trusting the underlying platform provider.
Server-side rendering of massive encrypted video and audio files too large to download locally for playback.
Research institutions and private companies can combine, analyze, and search proprietary data without exposing it to cloud vendors.
Real-world example
One university was using decommissioned supercomputer hardware for air-gapped research infrastructure. With confidential computing, they can now do the same work online, securely, with modern cloud capabilities. It is the equivalent of air-gapped systems without the drawbacks, and it works with external collaborators who would never have access to air-gapped systems.
The Multi-Party Collaboration Advantage
Multi-party computing is the fastest-growing application segment in the confidential computing market, and it unlocks a powerful capability: keeping data confidential not only from cloud vendors, but also from your collaborators themselves.
The same model applies across multiple industries where collaboration and confidentiality have always been in tension:
- Intelligence agencies working collaboratively across jurisdictions
- Financial institutions comparing fraud patterns without exposing customer data
- Healthcare systems analyzing patient outcomes across organizations
- Defense primes coordinating on classified programs across supply chains
You can collaborate to find the same answer without exposing your proprietary intelligence or intellectual property.
How This Fits Into Complete Security
Confidential computing complements existing security approaches rather than replacing them.
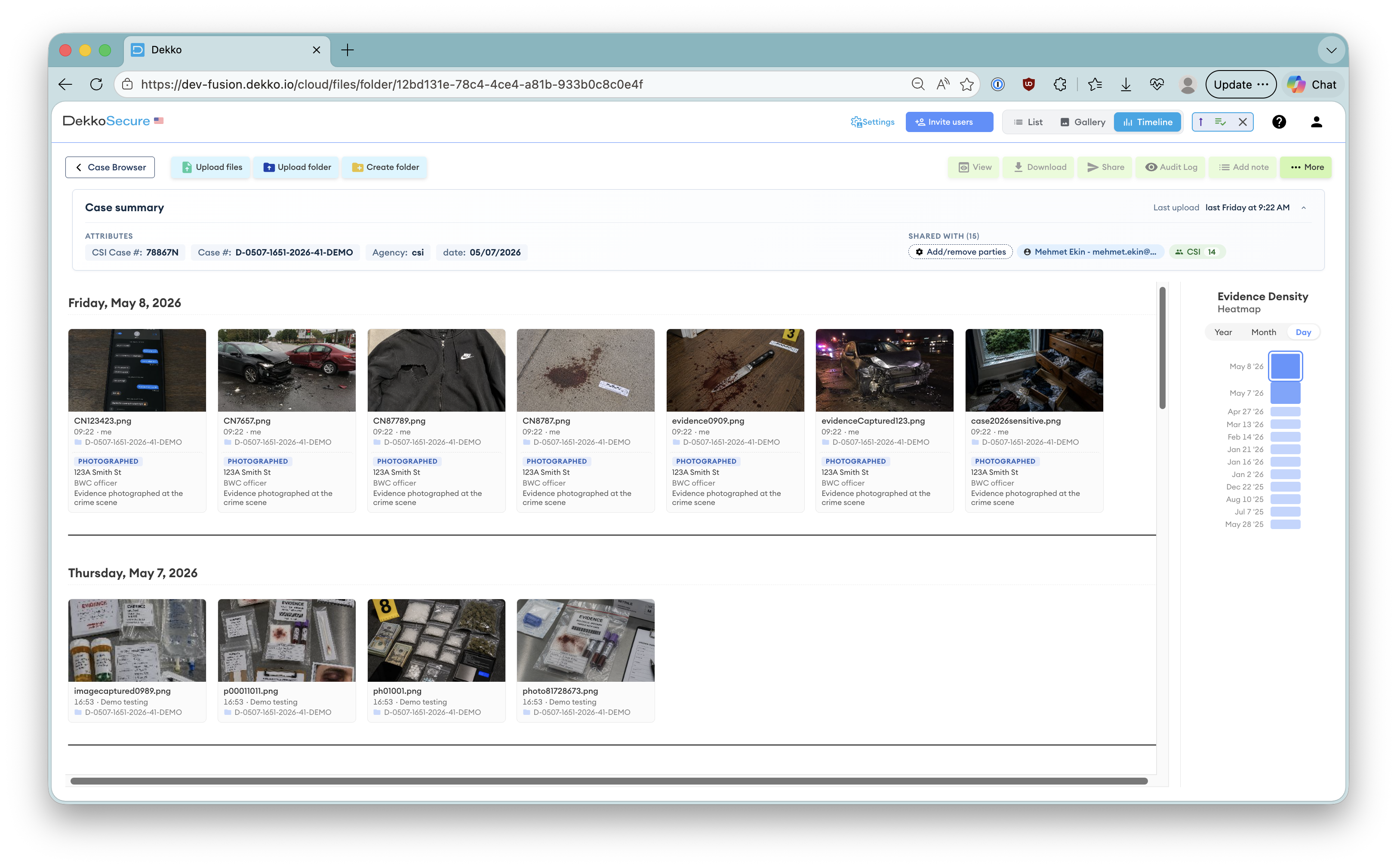
DekkoSecure has been building zero-knowledge architecture for more than a decade, starting with messaging, then file sharing, eSignatures, and video conferencing. All of these use client-side cryptography where the cloud was never trusted. Confidential computing extends those capabilities to server-side processing: document collaboration, multimedia rendering, and data manipulation and analysis.
A complete workflow example: a document can be authored in a confidential computing environment with multiple people collaborating, then shared using encrypted file sharing, signed with secure eSignatures, and discussed over encrypted video conferencing or messaging. Supporting video or audio materials can be played back in-app with secure server-side rendering. The entire collaboration lifecycle is protected.
One Question to Identify Your Use Case
Here is the simplest way to determine if confidential computing solves a problem for you:
The diagnostic question
What are you doing on-premises today that you wish you could do in the cloud, but cannot, because of confidentiality and security concerns?
That is your confidential computing use case.
The technology exists now through major cloud providers including AWS, Azure, and Oracle, who offer confidential computing infrastructure. Service providers like DekkoSecure deliver complete solutions built on that infrastructure.
Current limitations
Confidential computing is primarily focused on CPU-bound tasks. GPU-accelerated confidential computing exists for AI workloads and other graphics-intensive processes, but the technology remains cost-prohibitive for most organizations.
The cloud transformation journey for compute is following the same path as storage. Organizations that were once afraid to move files off-premises now routinely use cloud storage with confidence.
The same shift is happening with processing. Confidential computing is what makes it possible.
Common questions
Frequently Asked Questions
What is confidential computing in simple terms?
Confidential computing is a technology that keeps your data private even while it is being actively processed in the cloud. Most cloud security protects data when it is stored or being transferred, but leaves it exposed during processing. Confidential computing closes that gap by running workloads inside a hardware-based secure enclave where the data is encrypted even while being worked on, invisible to the cloud provider, the operating system, and anyone else on the infrastructure.
What is a Trusted Execution Environment (TEE)?
A Trusted Execution Environment, or TEE, is an isolated, hardware-protected area inside a processor where code and data can be processed securely. It encrypts both the CPU and RAM during computation, meaning nothing outside the enclave, including the cloud provider's own systems, can read what is happening inside it. TEEs are the core mechanism behind confidential computing, and are offered by major chip manufacturers including Intel, AMD, and ARM.
How does attestation work in confidential computing?
Attestation is a continuous verification process that confirms a TEE is running in a genuinely secure state. The enclave generates a cryptographic "measurement" of its own code and environment, which can be verified by an independent attestation service. If the environment has been tampered with or security has been disabled, the attestation check fails and processing halts automatically. This means you can verify that the hardware protecting your data is legitimate before you send any sensitive information into it.
What problems does confidential computing solve that encryption alone cannot?
Encryption protects data at rest (stored files) and in transit (data moving across networks), but data must be decrypted to be processed. That creates a window of exposure on the provider's servers. Confidential computing eliminates this window by encrypting data even while it is being actively computed on, inside the secure enclave. The provider never sees unencrypted data at any point, which is something traditional encryption cannot achieve.
Can confidential computing eliminate the need to trust cloud providers?
It significantly reduces the trust required. With confidential computing, you do not need to trust the cloud provider's staff, systems, or policies to keep your data private during processing — the hardware enforces that privacy technically. The provider supplies the infrastructure but cannot access what runs inside it. You still rely on the cloud provider for availability and the integrity of the hardware itself, but you no longer need to trust them with access to your data.
Who needs confidential computing?
Any organization that needs to process sensitive data in the cloud but cannot afford to expose it to the cloud provider. This includes government agencies handling classified information, healthcare organizations processing patient records, financial institutions running sensitive analytics, research institutions collaborating on proprietary datasets, and defense organizations working across supply chains. If you are currently keeping sensitive workloads on-premises solely because of cloud trust concerns, confidential computing is the technology designed specifically for your situation.
Which cloud providers offer confidential computing?
The three major cloud providers all offer confidential computing infrastructure: Microsoft Azure (Azure Confidential Computing), Amazon Web Services (AWS Nitro Enclaves), and Oracle Cloud Infrastructure. Each uses hardware-level TEEs to isolate workloads. Service providers like DekkoSecure build complete solutions on top of this infrastructure, handling the complexity of key management, attestation, and secure workflow design so organizations do not need to build it from scratch.