Law enforcement, national security, and defense entities operate where workflows are rarely linear, participants span multiple organizations with varying security clearances and jurisdictional authorities, and process failures can be catastrophic. Yet these mission-critical workflows are too often managed using collaboration tools designed for corporate efficiency, or manual processes that increase inherent risk.
A Fundamental Mismatch
The result is a fundamental mismatch between operational requirements and available infrastructure. Agencies need workflows that maintain security, evidentiary integrity, and accountability across organizational boundaries. Instead, they rely on improvised combinations of classified email, manual document routing, physical approvals, and ad hoc tracking that fragment workflows, introduce delays, and create accountability gaps precisely where mission success and prosecutorial outcomes demand seamless coordination.
Mission-critical workflows rarely occur within a single secure environment. Intelligence assessments might incorporate classified holdings from multiple agencies, require expert input from private sector partners, need review across multiple clearance levels, and inform operational decisions across allied governments. Multi-agency law enforcement investigations combine financial intelligence, signals intelligence, local evidence, and international contributions, each in separate systems with different security protocols.
Each system transition requires manual document handling, re-encryption, format conversion, and separate approval tracking, creating opportunities for version control failures, lost context, compromised chain of custody, and accountability gaps that undermine operational effectiveness and legal proceedings.
Four Systemic Challenges
Participants cannot see where documents are in approval chains, who has completed reviews, or what actions are pending, forcing email follow-ups and manual status tracking that slow time-sensitive operations.
When iterations occur across disconnected systems, outdated versions circulate, edits conflict, and the definitive current version becomes ambiguous, with strategic and legal consequences.
Audit trails manually assembled from email logs and access records across multiple systems fail when workflows must be forensically validated for legal proceedings or courtroom testimony.
When workflows span intelligence agencies, law enforcement, prosecutors, allied governments, and private sector partners, no unified view exists and coordination failures compound at every boundary.
The Strategic Consequences
These are not administrative inconveniences. The strategic consequences of inadequate workflow infrastructure are significant and compounding:
- Time-sensitive intelligence reaches decision-makers late and critical evidence reaches prosecutors after investigative windows close, potentially enabling adversary actions or compromising prosecutions.
- Coalition operations and joint investigations slow when infrastructure cannot support secure, efficient collaboration across organizational and national boundaries.
- Agencies default to restrictive sharing and over-classification, avoiding information sharing altogether even when intelligence could inform operations or evidence could support assessments.
- Analysts and investigators spend substantial time managing workflow coordination rather than conducting analytical or investigative work, representing significant opportunity costs.
- Producing the comprehensive documentation required for congressional oversight, legal review, and courtroom proceedings becomes a substantial burden, or reveals that definitive records do not exist, potentially compromising prosecutions.
Without structured workflows maintaining accountability and evidentiary integrity, agencies default to over-classification and restricted sharing, avoiding collaboration even when it could directly inform operations or support justice.
The AI Paradox
AI offers significant potential to accelerate mission-critical workflows, from intelligent routing and automated redaction to anomaly detection. But these capabilities become liabilities when implemented in infrastructure lacking robust security foundations.
AI analysis requires data to be decrypted and processed, creating exposure windows where classified intelligence and evidentiary materials exist unprotected in cloud environments. AI tools also create aggregated views that may violate compartmentalization principles and enable unauthorized access by cloud providers or AI vendors.
Organizations desperate for AI's efficiency gains are forced to choose between operational speed and security, often implementing AI in ways that compromise the very confidentiality, integrity, and accountability requirements that mission-critical workflows demand.
Without secure-by-design architecture, including zero-knowledge encryption, cryptographic integrity verification, and data sovereignty controls, AI assistance does not solve the security problem. It deepens it by creating sophisticated mechanisms through which sensitive information can be compromised, potentially undermining operational effectiveness and legal defensibility.
What Purpose-Built Infrastructure Must Provide
Managing mission-critical workflows requires purpose-built, secure-by-design technology infrastructure that treats workflow management as a core security, evidentiary, and operational capability. This infrastructure must provide:
- Unified environments spanning multiple classification levels and organizational boundaries
- Structured approval mechanisms respecting clearance levels and jurisdictional authorities
- Cross-organizational visibility while respecting need-to-know constraints
- Authoritative version control with forensic-grade integrity
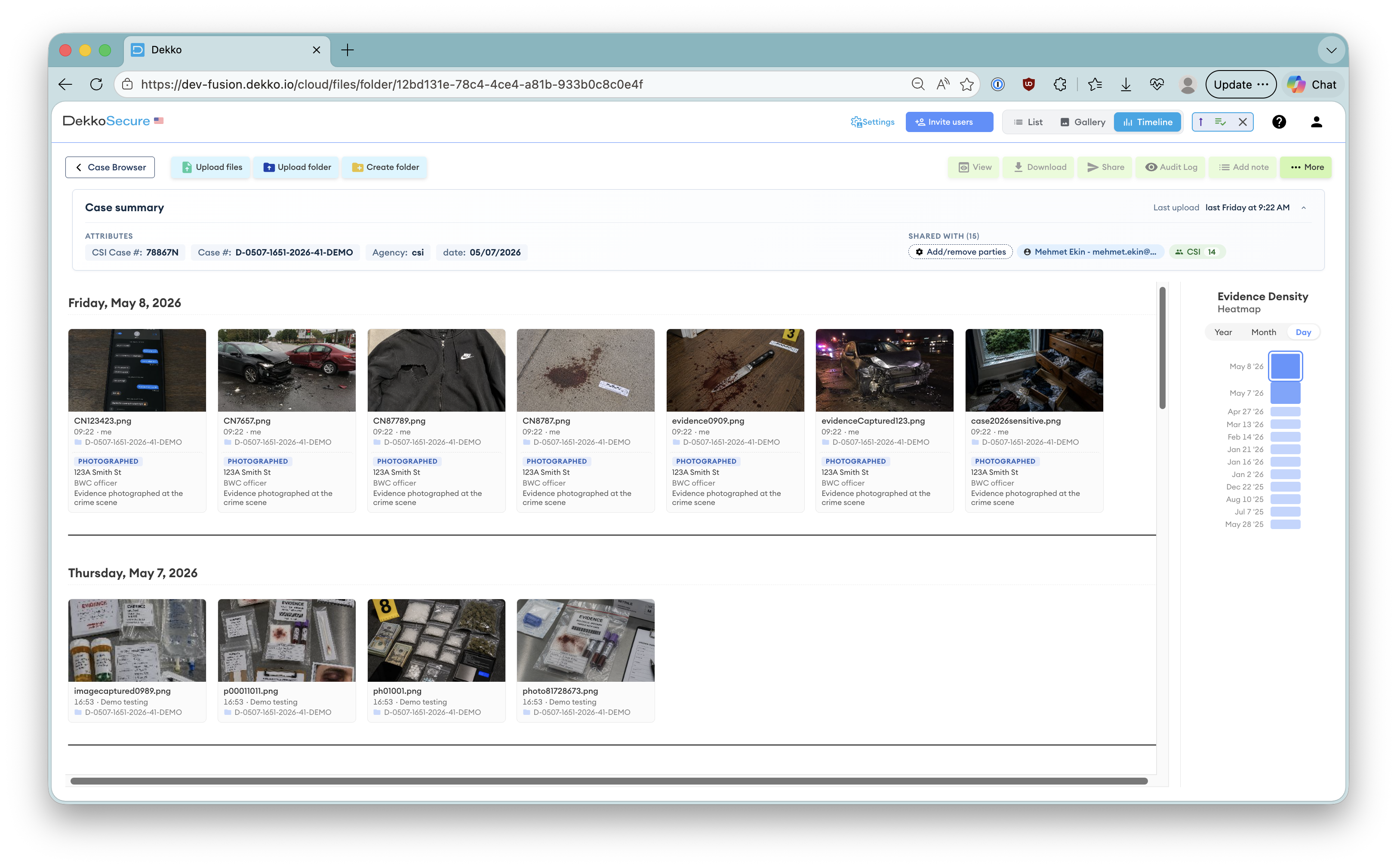
- Immutable audit trails capturing every action with guaranteed chain of custody
- Granular access control with instant revocation
- Seamless external participant onboarding across organizational boundaries
- Secure-by-design architecture embedding security principles at every layer so workflow infrastructure cannot itself become a vulnerability
Intelligence agencies and law enforcement organizations need collaboration infrastructure where workflow management is an embedded capability, maintaining security, preserving evidentiary integrity, enabling efficiency, and providing accountability throughout the mission lifecycle.
Without this infrastructure, workflows will continue to be constrained by tools designed for fundamentally different contexts, and national security operations and criminal investigations will remain fragmented and less effective than the threat environment and justice system demand.
Chief Executive Officer, DekkoSecure
Jacqui Nelson is the CEO of DekkoSecure, an Australian cybersecurity company specializing in zero-knowledge secure file sharing, digital evidence management, and secure collaboration for government, law enforcement, defense, and critical infrastructure sectors.