As organizations entrusted with sensitive information continue to face an evolving landscape of cyber threats, relying on outdated security models is no longer an option. Simply trusting that data is secure or relying on encryption alone is not enough. True security requires a holistic, multi-layered approach that goes beyond confidentiality and integrity to also ensure operational resilience and compliance.
At DekkoSecure, we have developed what we call the Six Pillars of Secure File Sharing: a comprehensive strategy that transforms how organizations protect their most valuable data. Each pillar addresses a distinct vulnerability, and together they form a complete security posture.
Zero-Knowledge Security
One of the most pervasive misconceptions about encryption is that simply having it means your data is protected. The details matter enormously. Just because a provider claims to use industry-standard encryption or follows security best practices does not guarantee your data is fully secure. If your cloud provider holds the encryption keys, your data is not truly private.
Zero-Knowledge Security ensures that encryption occurs before data ever leaves the device, with keys the provider cannot access. Even if a cloud provider is subpoenaed or breached, the data remains completely inaccessible to unauthorized parties.
Case study
A federal law enforcement agency responsible for managing classified intelligence was concerned about compliance risks due to the provider holding the encryption keys. By implementing zero-knowledge security, they ensured only authorized personnel could access sensitive files, helping them align with CJIS and national security requirements.
Automated Key Management
Encryption is only as effective as its key management strategy. Traditional key distribution processes are often manual, error-prone, and vulnerable to compromise. Poor key handling, especially when collaborating with external parties, introduces significant risk.
Automated Key Management eliminates these risks by automating the encryption process by default, reducing human error and ensuring that keys are never stored in plain text. This seamless and invisible handling of encryption keys ensures consistent protection, regardless of who you are sharing with.
Case study
A law enforcement agency dealing with sensitive digital evidence struggled with key distribution bottlenecks when collaborating with external stakeholders. By implementing automated key management, they significantly accelerated their workflows while eliminating the risk of mishandled encryption keys.
Zero-Trust Architecture
Legacy security models mistakenly assume that once someone is inside the network, they can be trusted. This is a dangerous assumption. Insider threats and credential compromises are among the leading causes of data breaches.
Zero-Trust Architecture challenges that assumption by enforcing continuous verification. Every access attempt is authenticated, authorized, and logged, with security policies applied dynamically rather than assumed at login.
Case study
A large financial institution came to us after suffering a breach due to compromised internal credentials. By deploying zero-trust architecture with continuous authentication, they significantly reduced insider risk and improved their overall security posture.
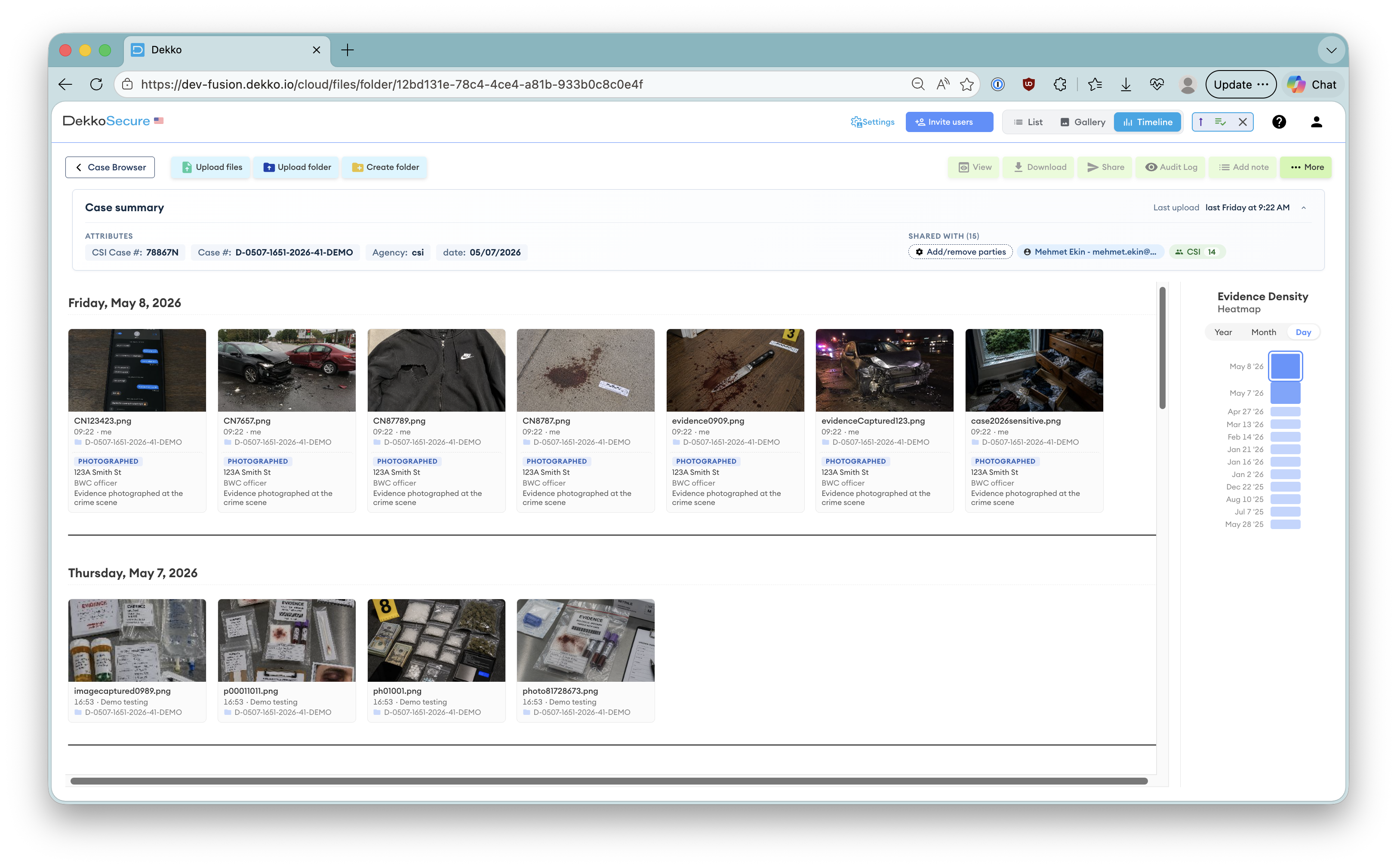
Comprehensive Audit Trails
While encryption protects data at rest and in transit, audit logging ensures accountability. Without an immutable record of file interactions, it is nearly impossible to detect insider threats or respond to security incidents effectively.
Comprehensive audit trails provide end-to-end tracking of file access, modifications, and sharing events, with tamper-proof logs that meet regulatory compliance standards. Integration with SIEM platforms further enhances visibility with real-time monitoring and alerting capabilities.
Case study
A defense contractor handling sensitive project data needed detailed monitoring of file access and sharing activities to meet strict compliance standards. By integrating audit trails with their SIEM platform, they gained real-time visibility into data interactions, enabling rapid detection of security anomalies and ensuring ongoing compliance with government requirements.
Granular Permission Controls
One-size-fits-all access controls create unnecessary vulnerabilities. Too many file-sharing solutions apply broad permissions uniformly across users, granting everyone access to download or edit files regardless of their actual role or need.
Granular permission controls allow organizations to define precise access rights for each user based on their role, project, and data sensitivity. Each user only has access to what they need: no more, no less.
Case study
A research organization sharing intellectual property with multiple external partners needed granular control over who accessed what data. By implementing per-user permissions on individual files and folders, they ensured that only authorized collaborators had access to specific datasets, greatly reducing the risk of leaks.
Highly Resistant Infrastructure
While confidentiality and access control are critical, availability is equally important. Secure file sharing must ensure zero downtime, even in the face of cyberattacks, system failures, or natural disasters.
Highly resistant infrastructure relies on geographically dispersed data centers, real-time replication, and redundant backups to ensure continuous data availability, even in the event of a cyberattack or other disruptions.
Case study
A critical government agency faced significant operational disruptions after a cyberattack. Thanks to multi-redundant data centers, they were able to restore services instantly without any data loss.
Implementing the Six Pillars
Use this checklist to assess your organization's current security posture against each pillar:
| Pillar | Key question to ask |
|---|---|
| Zero-Knowledge Security | Does our provider hold the encryption keys, or do we? Can they access our data under any circumstances? |
| Automated Key Management | Are our encryption keys managed securely and without manual handling or plain-text storage? |
| Zero-Trust Architecture | Do we verify every access attempt dynamically, or do we trust users once they are inside the network? |
| Comprehensive Audit Trails | Can we detect unauthorized access attempts in real time, and are our logs tamper-proof? |
| Granular Permission Controls | Are we limiting data access based on individual job roles and sensitivity levels, not broad groups? |
| Highly Resistant Infrastructure | Can we ensure continuous data availability in the event of a cyberattack, failure, or disaster? |
By adopting these six pillars, organizations can fortify their cyber resilience, meet stringent compliance requirements, and future-proof their data security strategies. The costs of failing to act are significant. A proactive security approach not only protects sensitive data but enables more efficient collaboration and workflows.
The future of data security is comprehensive and proactive. The Six Pillars of Secure File Sharing are designed to help you get there.
Chief Executive Officer, DekkoSecure
Jacqui Nelson is the CEO of DekkoSecure, an Australian cybersecurity company specializing in zero-knowledge secure file sharing, digital evidence management, and secure collaboration for government, law enforcement, defense, and critical infrastructure sectors.