When I first entered the technology sector, security was often treated as an afterthought — a checkbox to tick once the product was finished. Today, in an era where cybercriminals and state-sponsored actors are constantly probing for weaknesses, that approach simply will not do.
At DekkoSecure, we champion a different philosophy: security by design. This means embedding security considerations into every stage of development, rather than retrofitting solutions when vulnerabilities inevitably emerge.
The Cost of Bolted-On Security
Too many organizations still rely on layered defenses that sit outside the core application: perimeter firewalls, VPNs, or point-solutions for encryption. While these measures have their place, they leave critical gaps.
The perimeter fallacy
An attacker who bypasses the perimeter still sees unencrypted data in transit or at rest, and once inside, lateral movement is trivial. Worse still, reactive security products often hinder usability, leading teams to adopt workarounds such as sending sensitive files over email or USB drives simply because it is easier.
In one high-profile case, a government agency replaced 300,000 USB sticks with our platform, realizing both massive cost savings and a dramatic reduction in risk.
Security that impedes productivity will never be sustainable. And security that gets bypassed by workarounds protects nothing at all.
Designing Security into the Core
Secure by design means that security requirements drive the entire product lifecycle. At DekkoSecure, four principles guide how we build:
Before a single line of code is written, we identify the most likely and dangerous attack vectors for our users' data. Security architecture is defined before features, not after.
We never retain decryption keys. All encryption and decryption happen on the client side, so not even DekkoSecure can access your unencrypted files. No master keys, no exceptions.
Every file, message, or eSignature generates its own unique key and is cryptographically signed using the user's private key, preventing a single compromise from cascading across an entire dataset. These signing processes ensure non-repudiation and integrity without exposing private keys.
Every user action is authenticated, logged, time-stamped, and cryptographically verifiable in exportable reports, making it impossible to deny or obscure activity.
The Zero Trust Imperative
Zero trust reflects the reality that no component can be implicitly trusted. At DekkoSecure, our platform enforces strict authentication and authorization at every stage:
Case in Point: Government and Law Enforcement
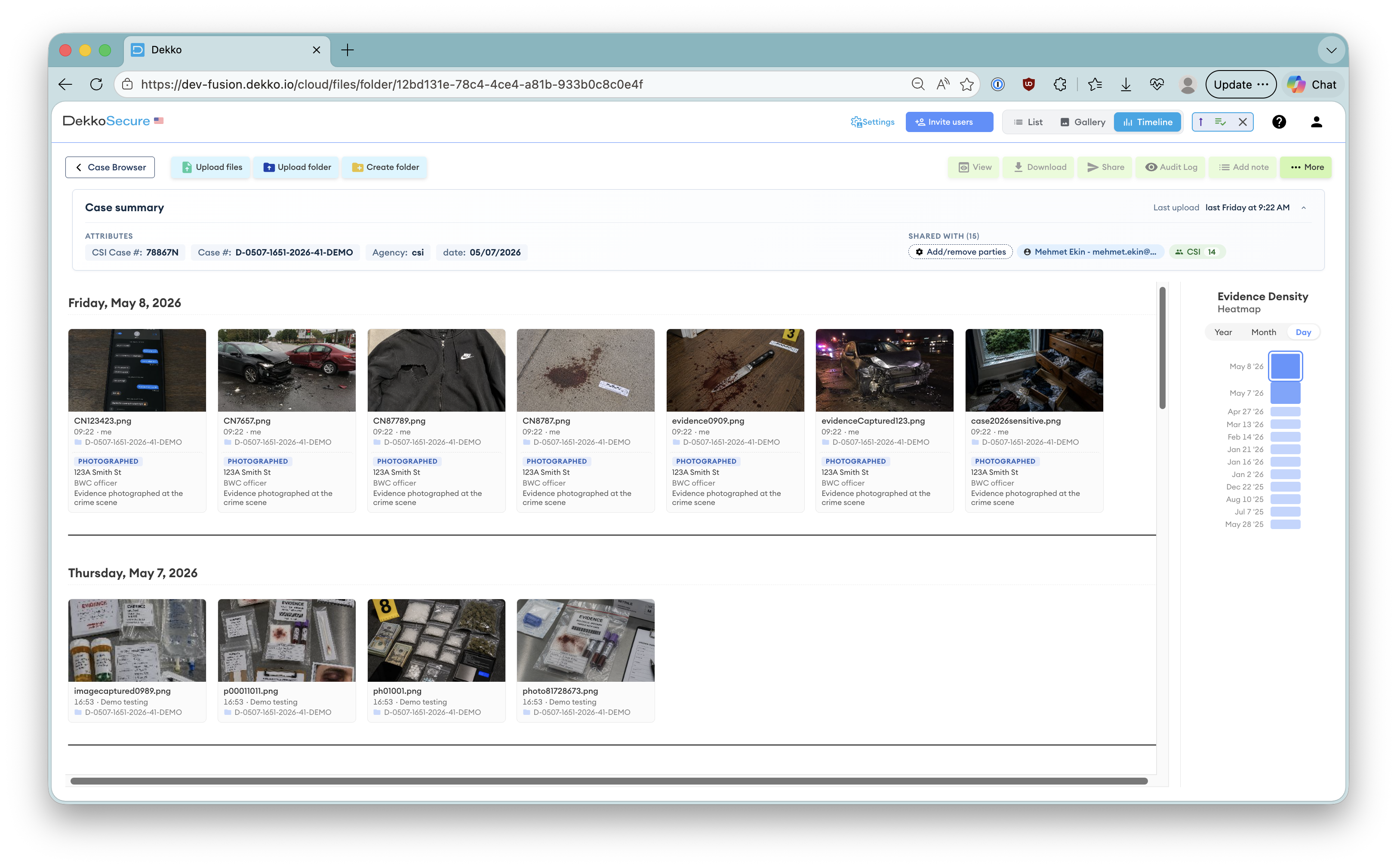
When we designed our secure Digital Evidence Management solution, we knew our customers demanded absolute assurance in both security and auditability. Law enforcement agencies cannot afford data leaks, misaddressed communications, or the legal ramifications of compromised evidence.
How secure-by-design avoids retrofit failure
By starting with these requirements rather than retrofitting security controls onto a generic collaboration platform, we built a system that meets law enforcement needs by architecture, not by policy.
- End-to-end encryption ensures each file remains confidential and unreadable by unauthorized parties
- Full auditability captures every interaction, meeting the strict standards of digital forensics
- Data sovereignty gives agencies full control over where their data is stored, critical for meeting national compliance obligations
Usability Is Not Optional
Security that impedes productivity will never be sustainable. Secure by design must also embrace user-centricity. When security seamlessly integrates with everyday workflows, adoption rises and so does overall organizational resilience.
Teams access the platform through a modern browser, removing the friction and risk of software installations across devices.
Users can edit documents together in real time and finalize approvals without exporting or emailing PDFs.
No need for third-party tools that expand your threat surface. Collaboration stays within the protected environment.
Building a Culture of Security
Technology alone is not enough. Embedding a secure-by-design mindset requires organizational commitment at every level:
Developers, security architects, and business stakeholders must collaborate from inception. Security cannot be delegated to a single team at the end of a development cycle.
Track mean-time-to-detect (MTTD), mean-time-to-respond (MTTR), and compliance posture alongside feature delivery. What gets measured gets managed.
Continuous testing against the latest threats keeps defenses sharp. At DekkoSecure, every new feature undergoes mandatory threat modeling and third-party verification by independent security labs.
The Future of Built-In Security
As organizations migrate more of their workflows to the cloud, the attack surface only expands. Traditional bolt-on tools will struggle to keep pace. Platforms that are secure by design can evolve securely:
We are researching and architecting support for PQC, including hybrid models combining traditional and PQC-ready schemes such as Kyber, ahead of the quantum threat horizon.
Machine learning models will help detect anomalies in real time, stopping threats before they gain a foothold without adding friction for legitimate users.
Secure APIs will let you integrate best-of-breed systems without undermining core security guarantees. Interoperability without compromise.
A Call to Action
If you are leading an organization that handles sensitive information, ask yourself these questions honestly:
- When was the last time your development process underwent threat modeling?
- Do you truly control your encryption keys, or have you handed them to a third party?
- Can you audit every user action with cryptographic assurance?
If the answers leave you uneasy, it is time to rethink your approach. Bolted-on security may deliver quick fixes, but only a foundation built on secure-by-design principles can withstand the evolving threat landscape.
True security is an enabler, not a barrier. When security is designed in from the first line of code, teams can collaborate with confidence rather than working around the controls meant to protect them.
Stop bolting on security. Start baking it in.
Chief Executive Officer, DekkoSecure
Jacqui Nelson is the CEO of DekkoSecure, an Australian cybersecurity company specializing in zero-knowledge secure file sharing, digital evidence management, and secure collaboration for government, law enforcement, defense, and critical infrastructure sectors.