Industry Insights
Strengthening Law Enforcement Data Security in the Digital Age
The necessity for law enforcement agencies to protect sensitive data has never been more critical. As the digital landscape evolves, technology continues to offer solutions that replace time-consuming and labor-intensive processes. But with scale comes risk, and safeguarding sensitive information against cyber threats and unauthorized access remains a growing concern.
Types of Sensitive Data Law Enforcement Must Protect
As the volume of highly sensitive data increases, so does the importance of protecting it. Within the law enforcement sector, this data includes:
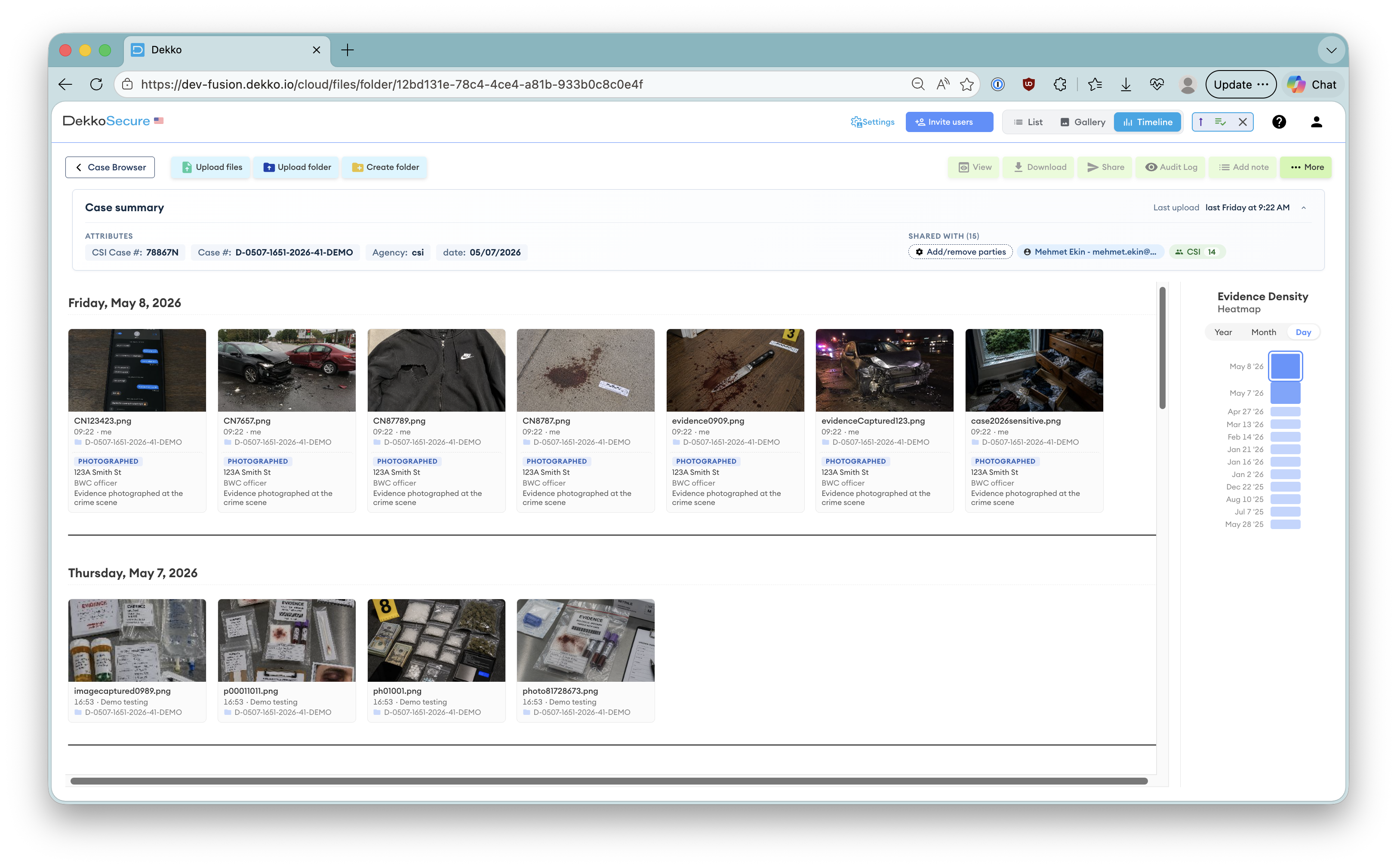
High-resolution images from active and high-profile investigations that require strict access controls.
Wiretap recordings and body-worn camera footage forming part of the evidentiary record.
Affidavits for search and arrest warrants that must remain confidential until execution.
Threat assessments, operational plans, and digital evidence supporting active investigations.
This data is essential for justice and operational success. Any unauthorized access can have severe consequences:
- Jeopardizing active investigations
- Exposing the identities of confidential informants
- Compromising officer safety
- Damaging public trust and an agency's reputation
- Undermining the ability to prosecute criminals effectively
Achieving Military-Grade Security in the Cloud
The key question is how this level of protection can be achieved in practice. The answer is cloud-based solutions built on end-to-end encryption combined with a Zero Trust and Zero Knowledge security framework. This approach provides military-grade protection that popular cloud solutions, email, hard drives, and physical courier simply cannot match.
Zero Trust means "never trust, always verify." Zero Knowledge ensures only authorized users ever have access to the data. End-to-end encryption ensures that not even the service provider can access it.
Together, these three principles form a security architecture purpose-built for environments where data compromise is not an option:
Every access request is verified against strict authentication and authorization policies. No user or device is trusted by default, regardless of location or prior access.
Only authorized users can ever access the data. Not the cloud provider, not the platform administrator, and not the service provider.
Encryption keys are managed by the platform in ways that ensure data remains encrypted at every stage: at rest, in transit, and at work.
Key Benefits for Law Enforcement Agencies
Adopting cloud solutions that incorporate a Zero Trust and Zero Knowledge framework delivers benefits that go beyond security alone:
-
🔒Enhanced security Zero Trust and Zero Knowledge security ensure data is always protected, with no gaps at any stage of the data lifecycle.
-
📈Scalability and flexibility Cloud platforms accommodate growing data demands and facilitate secure remote collaboration across agencies and jurisdictions.
-
💰Cost-effectiveness Cloud solutions reduce infrastructure costs by eliminating the need to purchase and maintain on-premises hardware.
-
✅Compliance and auditability Built-in alignment with standards including CJIS, combined with comprehensive audit trails that support accountability and chain-of-custody requirements.
Compliant, Encrypted, and Cyber-Secure
Adopting cloud-based solutions with end-to-end encryption, Zero Trust, and Zero Knowledge security provides protection against cyber threats and unauthorized access that legacy approaches cannot replicate. These technologies enhance security, scalability, and cost-efficiency while ensuring compliance with strict regulatory standards, enabling agencies to collaborate securely and with confidence.