Security Insights
How to Ensure Your Data Never Gets Breached
In a new era defined by digital and technical dominance, data protection has become one of the most critical issues of our time. Data is an incredibly valuable resource, and it is increasingly weaponized. The recent breaches of Dropbox Sign and MediSecure are prime examples of why protecting data at its core, not just at the perimeter, is the only approach that works.
What Is Secure-by-Design Technology and Why It Matters
For technology to qualify as secure-by-design, data protection must be integrated into the system from the very beginning, not added as an afterthought. Technologies built to this standard prioritize security at the foundational level:
- End-to-end encryption applied throughout the entire data lifecycle
- Granular access controls limiting exposure to only those who need it
- Strong authentication mechanisms verifying every access request
- Ongoing security updates built into the platform's operational cadence
By embedding this level of security into the foundation of a technology solution, organizations can establish a far stronger base for protecting their data within a data-centric security framework.
What Recent Breaches Reveal About Cybersecurity Risk
Two recent, high-profile incidents illustrate what is at stake when security is treated as a layer rather than a foundation.
An attacker compromised a back-end service account within Dropbox Sign's production environment. Because that account had elevated privileges, the attacker gained direct access to the customer database, exposing emails, usernames, phone numbers, hashed passwords, API keys, OAuth tokens, and MFA metadata for all Dropbox Sign users. Even individuals who had only received or signed a document without creating an account had their names and email addresses exposed.
All Dropbox Sign users affected. Third parties who never created an account also exposed.
The former national prescription delivery service provider MediSecure suffered a ransomware attack that encrypted its database server and exfiltrated approximately 6.5TB of data. The stolen records included names, dates of birth, addresses, Medicare numbers, healthcare identifiers, and prescription details. MediSecure subsequently went into voluntary administration. The breach is one of the largest in Australian history.
Approximately 12.9 million Australians affected. Nearly half the Australian population.
The consequences of these breaches extend beyond the immediate exposure of sensitive data. Organizations face reputational damage, loss of customer trust, regulatory scrutiny, and in MediSecure's case, complete operational collapse.
These breaches are a stark reminder that conversations between organizations and technology companies need to shift focus from securing the perimeters of the organization to securing the data itself.
The Scale of the Threat
These incidents are not isolated. A study by WatchGuard found that in 2023, there was a cyberattack every 39 seconds, amounting to more than 2,200 attacks per day. The three most prevalent forms were malware, ransomware, and phishing.
No organization is too large, too established, or too well-resourced to be exempt. The question is not whether an attack will be attempted but whether the architecture of your platform can withstand one.
How Zero Knowledge and Zero Trust Protect Your Data
While many platforms provide only partial security, a few specialized providers incorporate secure-by-design protocols that address the root cause of most breaches. The two most critical are Zero Knowledge and Zero Trust.
Every access request is authenticated and authorized before being granted, regardless of the user's identity, location, or prior access history. No one is trusted by default.
Encryption keys are managed transparently by the platform and are never accessible to the service provider. Data remains private and secure at every stage of its lifecycle, even if the provider's infrastructure is compromised.
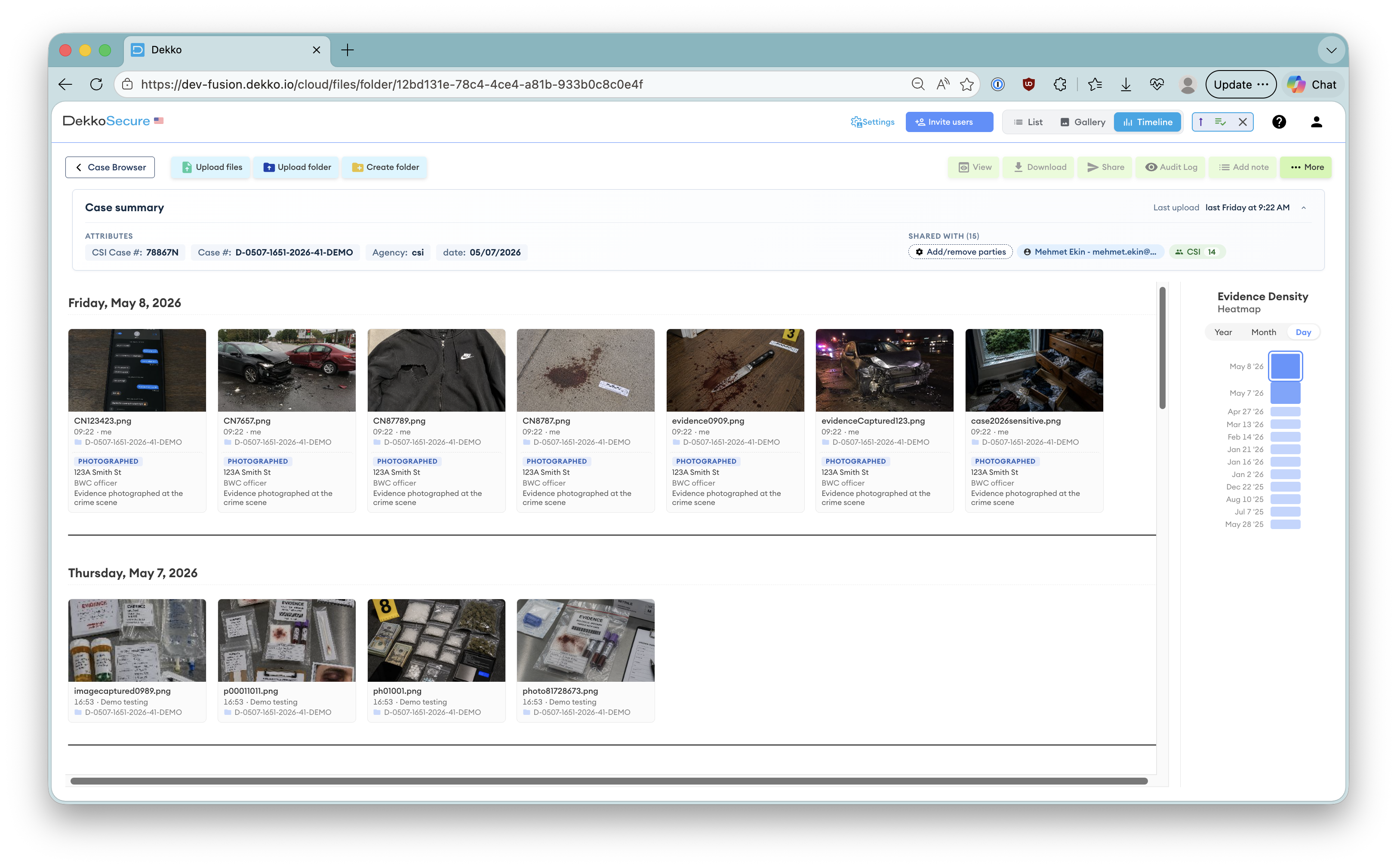
Together, these protocols prevent unauthorized access at the architectural level rather than relying on perimeter defenses that can be bypassed. This is why security-conscious organizations around the world choose platforms like DekkoSecure to protect their most confidential and sensitive data.
The Most Effective Posture Is Data-Centric
In this era of persistent and evolving cyber threats, investing in technologies that are secure-by-design is no longer optional. The most effective way to protect your organization and its data is to adopt a data-centric security posture and a platform where security is built in from day one, not bolted on after the fact.