Industry Insights
Comparison of Security Models Across Popular File-Sharing Solutions
CIOs, CSOs, and their teams are increasingly challenged to protect sensitive information while enabling seamless collaboration. The popularity of file-sharing platforms leads many to assume a high level of security exists by default. A closer look reveals that assumption is often wrong, and the consequences can be severe.
How Secure Are Popular File-Sharing Solutions?
Several popular file-sharing applications, both cloud-based and self-hosted, are used by organizations worldwide for internal sharing and external collaboration with clients and customers. To understand their true security posture, one question matters above all others: where is the data decrypted?
The key is to understand where the data is encrypted and, more importantly, where it is decrypted. For most popular platforms, that decryption happens on the provider's servers, where it is accessible to employees, system administrators, and opportunistic attackers.
Dropbox encrypts data in transit and at rest. However, Dropbox decrypts the data on its servers to provide the service, which means anyone with access to those servers, including Dropbox employees and opportunistic attackers, also has access to user data.
OneDrive uses the same security approach as Dropbox. User data is decrypted on Microsoft's servers, creating the same exposure risk. Anyone with server-level access can access customer data.
SharePoint is designed for enterprise use but shares the same security architecture as OneDrive. From a data protection standpoint, server-level access grants access to customer data, presenting the same fundamental limitation.
WeTransfer's security approach is similar to Dropbox and OneDrive. It is generally considered less secure than those platforms due to its lower level of audit controls and enterprise-grade access management features.
MOVEit is a self-hosted managed file transfer solution used by major global organizations. As a self-hosted product, organizations bear responsibility for keeping the software patched and current. In May 2023, that proved critical.
The Russian-affiliated Cl0p ransomware group exploited a critical SQL injection vulnerability in MOVEit Transfer software (CVE-2023-34362) before a patch was publicly available. The group automated exploitation across thousands of organizations simultaneously, making it one of the largest supply chain attacks on record.
Confirmed victims included the BBC, British Airways, Boots, PwC, Ofcom, Ernst and Young, and multiple US federal agencies including two Department of Energy entities. Many affected organizations were not even direct MOVEit users but were exposed through third-party providers such as payroll firm Zellis.
Side-by-Side Security Comparison
The table below compares how each platform handles the critical dimensions of data protection:
| Security feature | Dropbox | OneDrive | SharePoint | WeTransfer | MOVEit | DekkoSecure |
|---|---|---|---|---|---|---|
| Encryption in transit | Yes | Yes | Yes | Yes | Yes | Yes |
| Encryption at rest | Yes | Yes | Yes | Partial | Yes | Yes |
| Data invisible to provider | No | No | No | No | No | Yes |
| Zero Knowledge architecture | No | No | No | No | No | Yes |
| End-to-end encryption | No | No | No | No | No | Yes |
| Tamper-proof audit trail | No | Partial | Partial | No | Partial | Yes |
| CJIS compliance support | No | Partial | Partial | No | Partial | Yes |
| Self-hosted patch dependency | No | No | No | No | Yes | No |
Why Only Zero Knowledge Provides Complete Protection
Despite the measures employed by popular file-sharing platforms, a common limitation persists: the data must be decrypted on the provider's servers at some point in the workflow. This is the fundamental gap that Zero Knowledge security is designed to close.
In a Zero Knowledge security model, data can never be decrypted on the provider's servers. Only the owner of the data can decrypt it. This guarantees the highest level of protection regardless of what happens to the provider's infrastructure.
Your data remains secure even if the service provider is compromised. The provider has nothing to hand over because they cannot see it.
Without access to the data, insider threats are substantially reduced. Full auditability and visibility controls add an additional layer of accountability.
Zero Knowledge security supports compliance with HIPAA, CJIS, GDPR, and other data protection frameworks by design, not by policy.
How to Choose a Secure File-Sharing Platform
Your organization's specific security needs should guide the choice of a file-sharing platform. The right question to ask is straightforward: what are the consequences if our shared data is compromised?
If the data is highly sensitive or confidential, the only way to ensure its protection is to choose a platform built on Zero Knowledge security. Choosing a partially secure solution means accepting a substantial and ongoing risk.
The Standard Has Changed
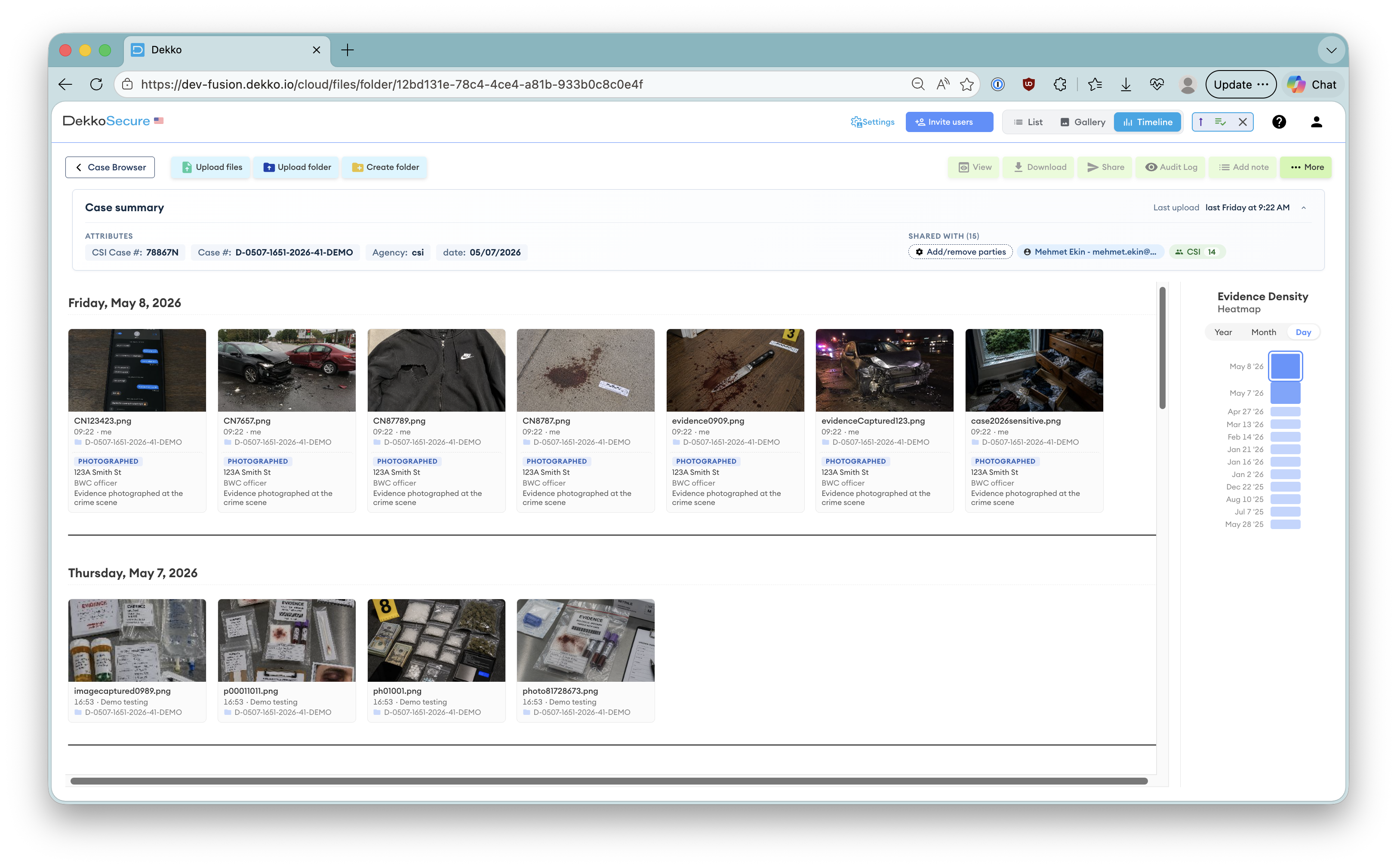
While the majority of vendors provide only partial security, specialized providers like DekkoSecure incorporate Zero Knowledge security, ensuring fully protected file storage and transfer. In environments where data compromise is not an option, partial security is no security at all.