Security Insights
End-to-End Encryption for Secure File Sharing
A dangerous myth persists in the digital workspace: that strong security and seamless collaboration are fundamentally at odds. This misunderstanding has forced organizations into risky and unnecessary compromises. The truth is that it is a false choice, and the technology to prove it already exists.
Beyond Partial Protection
True end-to-end encryption means data is encrypted at rest, in transit, and at work. It is never exposed to the servers where it is stored or to the service providers facilitating storage and transmission. Many vendors claim that true E2EE cannot be a shared technology, asserting that it is almost impossible to implement reliably.
The risk of "almost E2EE"
Easier-to-implement solutions that fall short of true E2EE leave critical vulnerability gaps. While they may encrypt data in transit, the data is left exposed on the vendor's servers during sharing, processing, and transfer. This creates opportunities for unauthorized access and data breaches, particularly when the data is sensitive or confidential.
The table below shows how true E2EE differs from partial protection approaches that most file sharing vendors offer today:
| Protection layer | Partial ("almost E2EE") | True E2EE |
|---|---|---|
| Data in transit | Yes | Yes |
| Data at rest | Sometimes | Yes |
| Data at work (during processing) | No | Yes |
| Invisible to service provider | No | Yes |
| Invisible to administrators | No | Yes |
| Single credential cannot expose all data | No | Yes |
Building Collaboration Based on Trust
When team members know their shared information remains protected throughout the entire cycle, from creation through collaboration to storage, they gain confidence in sharing even the most sensitive data. Without the fear of exposure to servers, third parties, or system administrators, collaborators communicate more openly and more efficiently.
Many security-conscious organizations avoid cloud solutions entirely due to a lack of trust. Their resistance is understandable. Without true E2EE, their data is vulnerable in the cloud. But bypassing the cloud while continuing to rely on manual and legacy sharing practices is also a risky practice.
In the presence of true E2EE, these concerns dissolve. Data remains inaccessible to the cloud provider, automatically removing the trust barrier, because only authorized and authenticated parties ever have access to shared data.
The Technical Reality
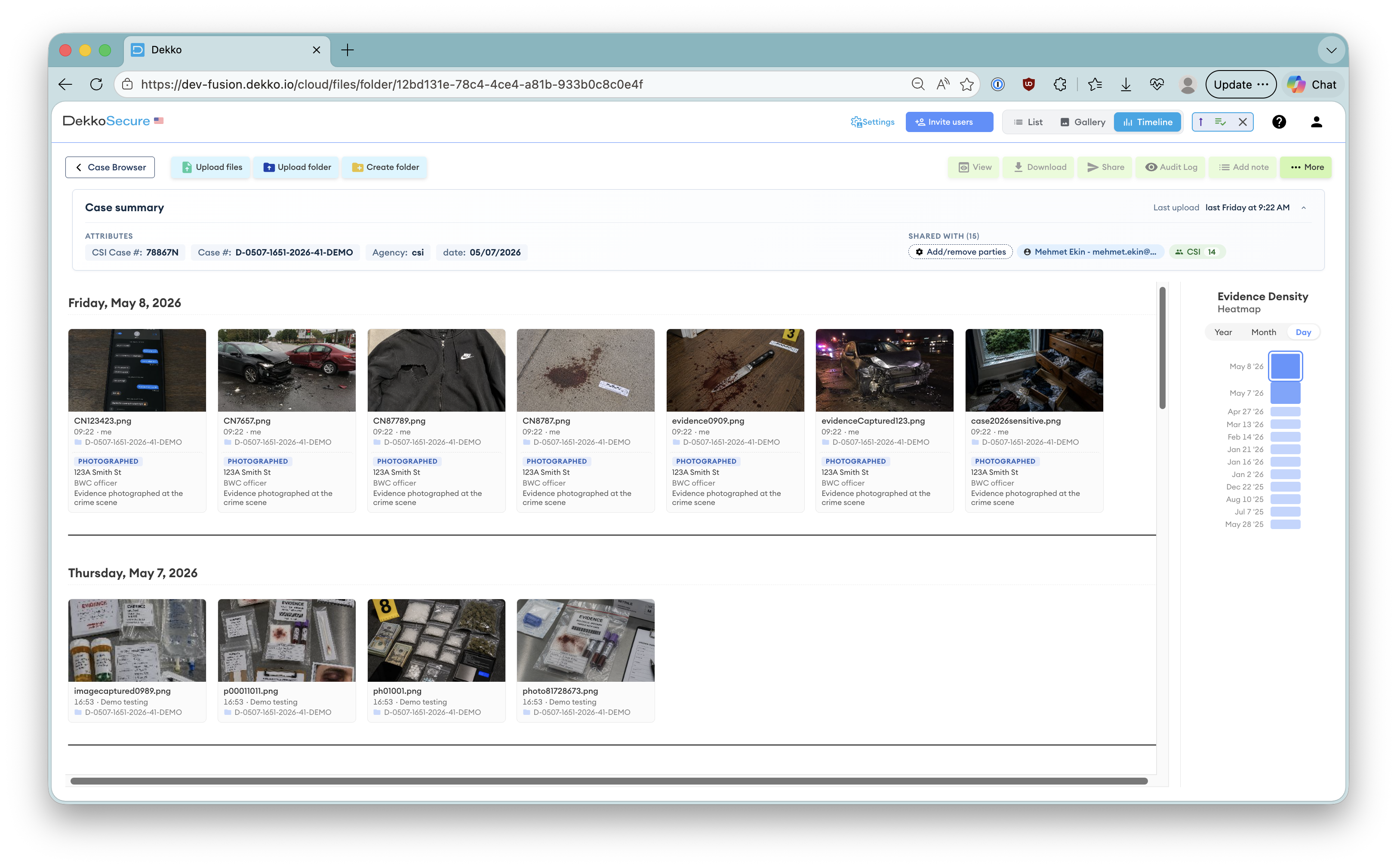
At DekkoSecure, we have developed collaboration solutions that provide true E2EE while maintaining a seamless user experience for secure file sharing and transfer. The platform features transparent encryption key management, allowing users to collaborate easily and securely without manually managing encryption keys.
Combined with zero-trust architecture, which always requires authentication and authorization for information access, these elements create true zero-knowledge security. This means not even DekkoSecure can access your data.
- Share files of any size or type through secure file sharing
- Communicate and collaborate without security steps disrupting workflow
- No manual encryption key management required
- Zero-knowledge security: even DekkoSecure cannot read your plaintext data
- No central authority or single key can bypass the encryption
Regulatory Advantages
True E2EE significantly reduces data breach risks by closing the common vulnerabilities most often exploited across transfer, storage, and collaboration. More importantly, it prevents the catastrophic scenario where a single stolen high-privilege credential leads to complete data exposure.
In traditional centralized systems without E2EE, all data resides in one place accessible with broad administrator permissions. If an attacker compromises one senior account, they gain access to everything. When each piece of data is separately encrypted end-to-end, a compromised credential no longer unlocks the entire vault. At most, one piece of data is exposed while all other data remains secure.
Two major breaches illustrate precisely what is at stake when E2EE and strong access controls are absent:
Case study
Medibank (2022)9.7 million patient records were exposed after stolen VPN credentials gave an attacker broad access to centralized databases. The breach was compounded by the absence of multi-factor authentication, a critical defect Medibank had been warned about two years prior.
Case study
Genea Fertility (2025)The Termite ransomware group exploited a Citrix server vulnerability and accessed 27 servers containing nearly 1TB of sensitive patient data, including medical histories and Medicare numbers. The stolen data was reportedly stored unencrypted.
As privacy regulations increasingly demand data protection by design and by default, technology must be built from the ground up with a security focus, not with security added as an afterthought. DekkoSecure's E2EE zero-trust platform ensures information stays protected at all times by technical means rather than policy promises.
In practice, this means audits are easier to pass and privacy requirements are met proactively. Data security is assured by design, not dependent on trust alone.
The Collaborative Future
Imagine a future where E2EE becomes the standard for collaborative work. This technology exists today.
Organizations share sensitive information remotely without relying on outdated methods like USB drives or encrypted hard drives.
Teams work on highly confidential projects from anywhere, with security that enhances rather than restricts collaboration.
Innovation accelerates when security concerns no longer create friction in the creative process.
Changing Perspectives
An educational gap represents the final barrier to widespread adoption of E2EE-enabled collaboration technologies. Once organizations understand that true E2EE protects information without impeding workflow, the value proposition becomes self-evident.
Security and collaboration are not competing interests. With seamlessly integrated E2EE, they are natural allies. The wall between them has been taken down.
Data remains protected while simultaneously becoming more accessible to authorized team members. That is not a compromise. That is what modern security is supposed to look like.
Common questions
Frequently Asked Questions
What is "true" end-to-end encryption (E2EE), and how is it different from "almost E2EE"?
True E2EE keeps data encrypted at rest, in transit, and at work, so it is never exposed to storage or transmission servers, or to the service provider. "Almost E2EE" tools often encrypt data in transit but decrypt it on vendor servers during sharing or processing, leaving critical gaps where unauthorized access or breaches can occur.
How can strong security like E2EE coexist with seamless collaboration?
When E2EE is designed in from the start, collaboration does not suffer. With transparent key management and a zero-trust approach that always requires authentication and authorization, users can securely share files of any size or type, communicate, and collaborate without security steps disrupting their workflow.
Why do some organizations avoid cloud collaboration, and how does true E2EE address their concerns?
Many avoid the cloud because, without true E2EE, data can be exposed to providers, servers, or administrators. Genuine E2EE removes this trust barrier by ensuring only authorized and authenticated parties can access data. Even the provider cannot see plaintext. This mitigates risk more effectively than sticking with manual or legacy sharing methods.
What regulatory and risk-reduction advantages does true E2EE provide?
True E2EE closes common breach vectors across transfer, storage, and collaboration, and prevents a single high-privilege credential from exposing everything. Instead, compromise is limited to at most one piece of data. This contrasts with centralized, non-E2EE systems implicated in major breaches like Medibank and Genea. Because it embodies data protection by design and by default, E2EE simplifies audits and aligns with privacy requirements proactively.
How does DekkoSecure implement E2EE while keeping the experience intuitive?
DekkoSecure provides true E2EE with transparent encryption key management, a zero-trust architecture, and zero-knowledge security, so not even DekkoSecure can access plaintext, and no central authority or single key can bypass encryption. Users can securely share and collaborate on any file type or size without workflow friction.