Trust is fragile. In digital evidence management, when it breaks, the consequences can be catastrophic. Careers, case outcomes, and public confidence hang in the balance. Yet too often, the systems we rely on to safeguard critical investigative material fail precisely when they are most needed.
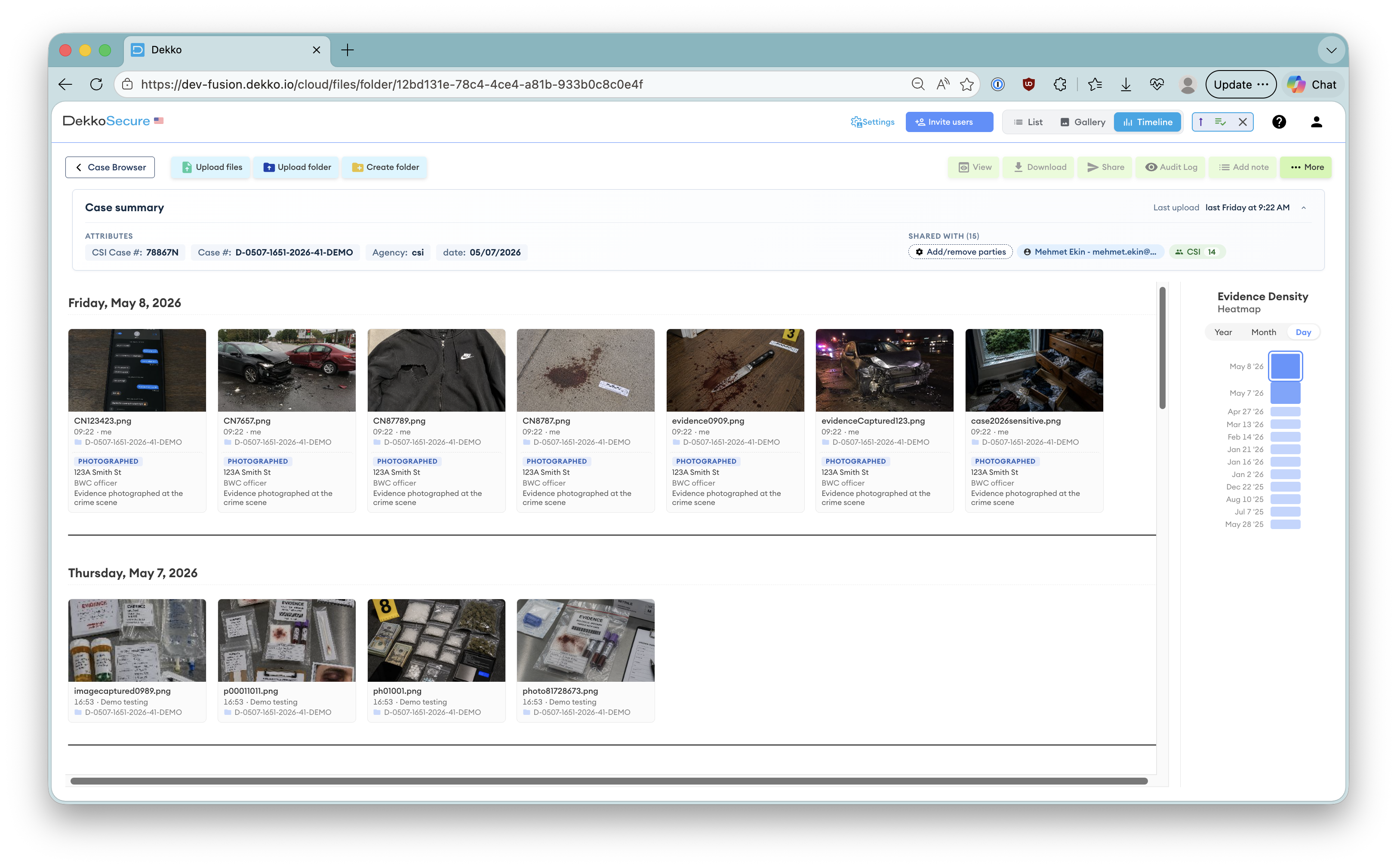
As law enforcement agencies around the world accelerate their digital transformation, managing digital evidence securely, efficiently, and reliably has become an operational imperative. Body-worn cameras, cell phone extractions, surveillance footage, and digital communications now form the backbone of modern policing. But the platforms designed to manage this evidence frequently fall short in key areas.
Having worked alongside law enforcement agencies to develop secure, purpose-built digital solutions, I have witnessed firsthand how existing systems introduce operational risks, expose agencies to cyber threats, and jeopardize the integrity of evidence. And while some compromises made by market leaders may seem inconsequential at first, the consequences of employing technology that does not prioritize security grow dangerously clear as agencies attempt to scale.
The Non-Negotiables for Digital Evidence Management
Before examining where popular solutions fall short, it is important to agree on what an effective digital evidence management system must deliver:
Where Market Leaders Are Falling Short
Feedback from agencies my team has spoken with highlights that many of today's popular digital evidence management platforms compromise on one or more of these essential requirements:
Security gap
Cloud-first without end-to-end encryptionA very popular provider prioritizes ease of deployment but sacrifices security by not employing end-to-end encryption. In certain scenarios this potentially allows vendor access to the data, introducing confidentiality and chain of custody vulnerabilities.
Integration gap
Limited APIs, isolated systemsOther solutions prioritize price competitiveness but lack mature integration capabilities. Limited APIs result in isolated systems, forcing investigators to manually transfer data and manage separate audit streams for each system.
Infrastructure gap
On-premises legacy, unfit for cloudA provider with long on-premises history remains ill-suited for cloud migration and hybrid environments. Their infrastructure-heavy approach demands high technical overhead and locks agencies into expensive, inflexible models.
Scale gap
Forensic depth without operational scaleOne high-profile provider excels at forensic analysis but struggles to manage high-volume evidence types like body-worn video at scale. Specialist depth does not always translate to operational breadth.
These weaknesses rarely surface during procurement. They emerge over time, typically under operational pressure, during major incidents, or when agencies attempt to modernize their workflows.
The Hidden Security Compromise Few Acknowledge
The most critical flaw across platforms lies in their fundamental security model. Most digital evidence management systems secure data using a methodology that relies on the vendor's internal security practices, leaving the underlying database of evidence vulnerable should the vendor experience a breach.
Should a malicious actor, vendor staff member, or rogue administrator gain access to the database layer, they can potentially also access highly sensitive evidence. This is not a theoretical issue. It is a potential reality.
The only way to truly guarantee data protection is to implement a system that is end-to-end encrypted and delivers a zero-knowledge security model, ensuring that not even the platform provider can access evidence under any circumstances.
Surprisingly, this type of security model remains the exception, not the rule. Most systems still rely on procedural controls and application-layer permissions, safeguards that can too easily be bypassed. Most, if not all, of the very public security breaches affecting the sector would have been prevented had a more sophisticated security model been employed.
The Integration Problem the Industry Does Not Talk About
Equally concerning is how poorly many evidence management systems integrate with operational workflows. Evidence management is one node in a larger investigative process, requiring seamless connection with:
While most vendors claim integration capabilities, they typically fall short in three critical areas:
- Authentication federation for secure, seamless single sign-on across connected systems
- Metadata standardization to maintain consistent evidence records across platforms
- Workflow automation to reduce reliance on inefficient, error-prone manual processes
What a Better Solution Looks Like
A truly modern digital evidence management platform requires a fundamentally different architecture. This is not a wish list. It is what responsible, future-ready digital evidence management demands:
- Zero-knowledge security with encryption at the data's origin and keys managed exclusively by the agency
- Immutable, blockchain-inspired chain of custody logs capable of withstanding courtroom scrutiny
- API-first integration frameworks enabling clean, reliable connections to all core agency systems
- Adaptive access controls that adjust permissions based on case status, security classifications, and investigator roles
- Hybrid deployment options allowing agencies to balance security, accessibility, and cost as operational needs evolve
Where Law Enforcement Agencies Should Focus Next
For agencies reviewing their evidence management posture or considering new platforms, the priorities are clear:
Conduct realistic, scenario-based security assessments. Do not settle for compliance checklists.
Test integrations under operational load rather than in vendor-controlled demonstrations.
Consider total cost of ownership, operational overhead, and future scalability risks before committing.
Avoid repurposed general-purpose file sharing platforms in favor of law enforcement-specific solutions.
Work with technology partners who deeply understand the operational, legal, and evidentiary realities of modern policing.
The future of digital evidence management belongs to solutions built from the ground up with security, chain of custody, and interoperability as their core design principles, not retrofitted to check procurement boxes.
As more cases hinge on digital evidence, its security and integrity must be unimpeachable. The systems we rely on to protect that evidence should be no less reliable than the officers who gather it.
Law enforcement deserves nothing less.
Chief Executive Officer, DekkoSecure
Jacqui Nelson is the CEO of DekkoSecure, an Australian cybersecurity company specializing in zero-knowledge secure file sharing, digital evidence management, and secure collaboration for government, law enforcement, defense, and critical infrastructure sectors.