Industry Insights
Chain of Custody: Data Integrity for Justice
When a photo is captured at a crime scene, it must be the same one that is presented in court.
When a bystander records a video, it must be the same one that the jury sees.
When an investigator captures an audio file, it must be the same one that the judge hears.
In digital evidence, one truth defines the chain of custody: the unbroken record of where evidence has been, who handled it, and whether it has changed. Every moment of uncertainty between capture and presentation can become a point of legal challenge.
The Science of Verification
To prove that a file has remained unaltered, digital forensics teams rely on hash functions and hash checks.
A hash function is a mathematical process that converts the contents of a digital asset into a unique digital fingerprint: a string of characters that will always be identical for that exact file. Even the smallest change produces a completely different result.
The commonly used SHA-2 hash function generates a 64-character fingerprint. For any given file, this output is always identical — until the file changes, at which point the output changes entirely.
Changing a single pixel, trimming one frame, or editing one word produces a completely different hash string.
Once a hash has been generated, investigators can later run the same function on the file and perform a hash check: comparing the original hash against the new one. If they match, the file is identical. If they differ by a single character, something has changed.
In court, a matching hash check is one of the few absolute proofs of digital integrity. It allows investigators, prosecutors, and defense teams to independently confirm a file is exactly the same as when it was first collected.
When the Chain Breaks
Detective Smith records body-worn video of an arrest. No hash is generated at capture.
Footage is copied to a desktop, then to a USB drive for the lead investigator. No transfer log is created.
Another copy is made for the attorney's office, who uploads the file to an online sharing tool for defense access. No audit trail. No recorded hash.
Defense argues: "There is no proof this video is the same one captured on the day. It could have been edited."
Without a verifiable chain of custody, the judge admits the footage only for limited use. A key piece of evidence loses its weight — not because of what it showed, but because the process failed to guarantee its authenticity.
The New Challenge for Digital Evidence Management
The issue of chain of custody has grown more complex with the rise of digital evidence management systems that include features for analysis, enhancement, and watermarking. These capabilities can add operational value, but they disrupt the most critical principle in the justice process: the integrity of the original file.
Changes introduced by enhancement features will never pass a hash check. As a result, modified files may be ruled inadmissible if there is any doubt that the version presented differs from the one originally captured. There are already examples of digital evidence management platforms being restricted or excluded from legal use precisely because their built-in features introduce the potential for modification, even if those features are never used.
"Accurate judgements and fair assessments in the legal system depend on absolute confidence that evidence has not been tampered with."
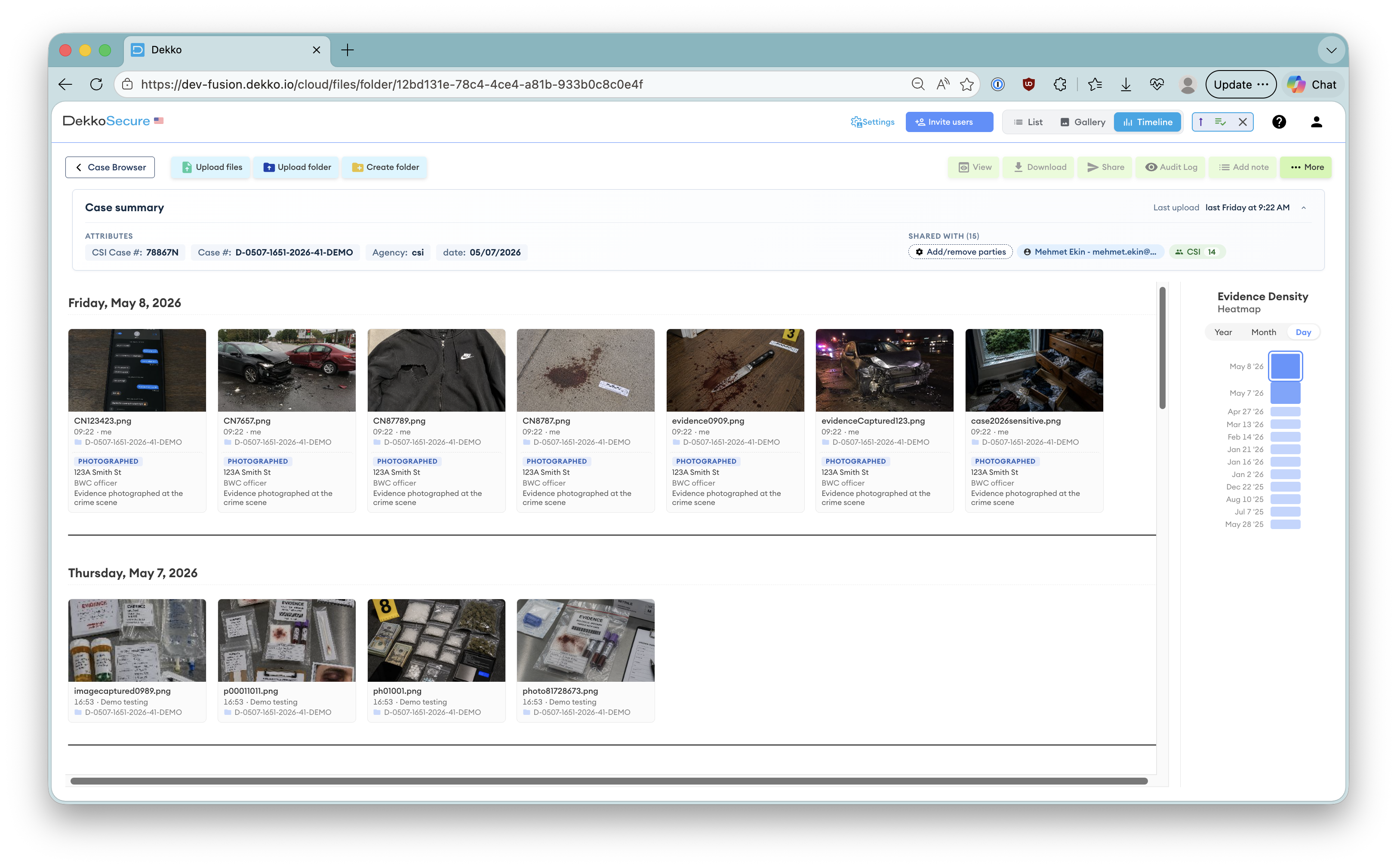
The Role of Centralization
Modern digital evidence management systems promise convenience: cloud storage, search, enhancement, and watermarking. But these same capabilities can threaten admissibility if they allow untracked modification or decentralized handling.
True integrity demands centralization. All evidence must enter a controlled environment the moment it is collected, and every subsequent action must be governed by the same system:
-
Immutability Every file is hashed at the moment of ingestion. No modification is possible without detection.
-
Auditability Every access, transfer, and download is logged with a timestamp and user identity. No action goes unrecorded.
-
Chain continuity No copy of a file should ever exist outside the auditable ecosystem. The chain is only as strong as its weakest transfer.
-
Transparency All parties — investigators, prosecutors, and defense — can independently verify the integrity of any file at any time.
Why It Matters
The goal of any justice process is accuracy: ensuring decisions are made on untainted facts. If the evidence itself cannot be trusted, the foundation of fairness collapses.
Centralized, verifiable digital evidence management is not simply good practice. In a world where a single pixel can alter a verdict, it is the last line of defense between truth and doubt.
Only a system built around immutability, auditability, and transparency can protect justice from uncertainty. What was captured must be what is presented. Nothing more. Nothing less.