Security Insights
Beyond SFTP: Zero-Knowledge and End-to-End Encryption
SFTP is widely used for secure file transfer, but securing the channel is not the same as securing the data. For organizations handling sensitive information, that distinction matters more than most people realize.
What Is SFTP?
SFTP, or Secure File Transfer Protocol, is a network protocol that provides secure file access, file transfer, and file management over any reliable data stream. Designed by the Internet Engineering Task Force (IETF) as an extension of the Secure Shell (SSH) protocol version 2, it is commonly used for transferring files securely between computers over the internet, managing remote files, and automating file transfers in business environments.
Despite its security benefits, SFTP has several limitations that organizations should understand before relying on it for sensitive data workflows.
- It requires technical knowledge to set up and maintain, often requiring server configuration and key management.
- Performance can be slow for large file transfers due to encryption overhead.
- User management is complex, especially for organizations with changing personnel.
- SFTP lacks built-in collaboration features, making it difficult for multiple users to work on files simultaneously.
- It provides limited visibility into file activities and may not meet compliance requirements for sensitive industries without additional tools.
Why SFTP Falls Short
SFTP encrypts data in transit, creating the impression of security. But this protection is incomplete. The protocol's fundamental limitation is straightforward: it secures the channel, not the data itself.
Think of SFTP like sending a letter in a sealed envelope with no way to tell if an unintended third party opened it, read it, and resealed it before delivery.
The connection is protected, but what happens before upload or after download? SFTP verifies data integrity during transmission, but provides no mechanism to detect changes made before a file is uploaded or after it is downloaded. For organizations handling sensitive data, this creates unacceptable risk.
SFTP also lacks cryptographically sealed audit trails. While system logs can be enabled, they are not tamper-proof. A compromised administrator or attacker with access can erase or modify these logs, leaving no reliable forensic evidence.
Most concerning is that once an SFTP connection is established, the server assumes the authenticated user is legitimate throughout the session. This creates vulnerability to credential theft and session hijacking.
Shifting to Data-Centric Security
To address these limitations, organizations must make the fundamental shift from channel security to data-centric security. The data itself must be protected regardless of where it resides or how it is transferred.
In a zero-knowledge security model, every file and every user interaction is encrypted with end-to-end encryption. The data is never exposed to any third party, not even the service provider. This approach ensures protection throughout the entire data lifecycle.
Encryption must follow the data, not just secure the network. This principle forms the foundation of modern security architectures that protect against today's sophisticated threats. The most robust approaches combine zero-trust with zero-knowledge principles:
Enforces identity verification and least-privilege access, never assuming anyone is authorized without verification.
Eliminates reliance on third parties for data security. Even system administrators cannot access plaintext data.
Together, these measures create a mathematically verified security model that is effectively breach-proof when properly implemented.
Implementation Without Complexity
Implementing comprehensive security no longer means burdening your technical teams. Modern solutions automate key security functions while maintaining usability. For organizations transitioning from legacy SFTP systems, the following best practices minimize disruption while maximizing security:
-
1
Adopt end-to-end encryption from day one, ensuring data remains protected throughout the transition.
-
2
Use cryptographically signed audit trails that automatically document every file access, transfer, and modification without manual logging.
-
3
Integrate multi-factor authentication with single sign-on systems to provide strong identity verification without constant re-authentication.
-
4
Implement identity-based access control to replace server-based permissions.
-
5
Ensure that security does not come at the expense of usability. Solutions must be intuitive enough that users do not seek workarounds.
-
6
Plan a phased migration that prioritizes your most sensitive data while maintaining operational continuity.
Industry-Specific Security Risks
Nearly every industry handling sensitive information faces data security risks when relying solely on SFTP:
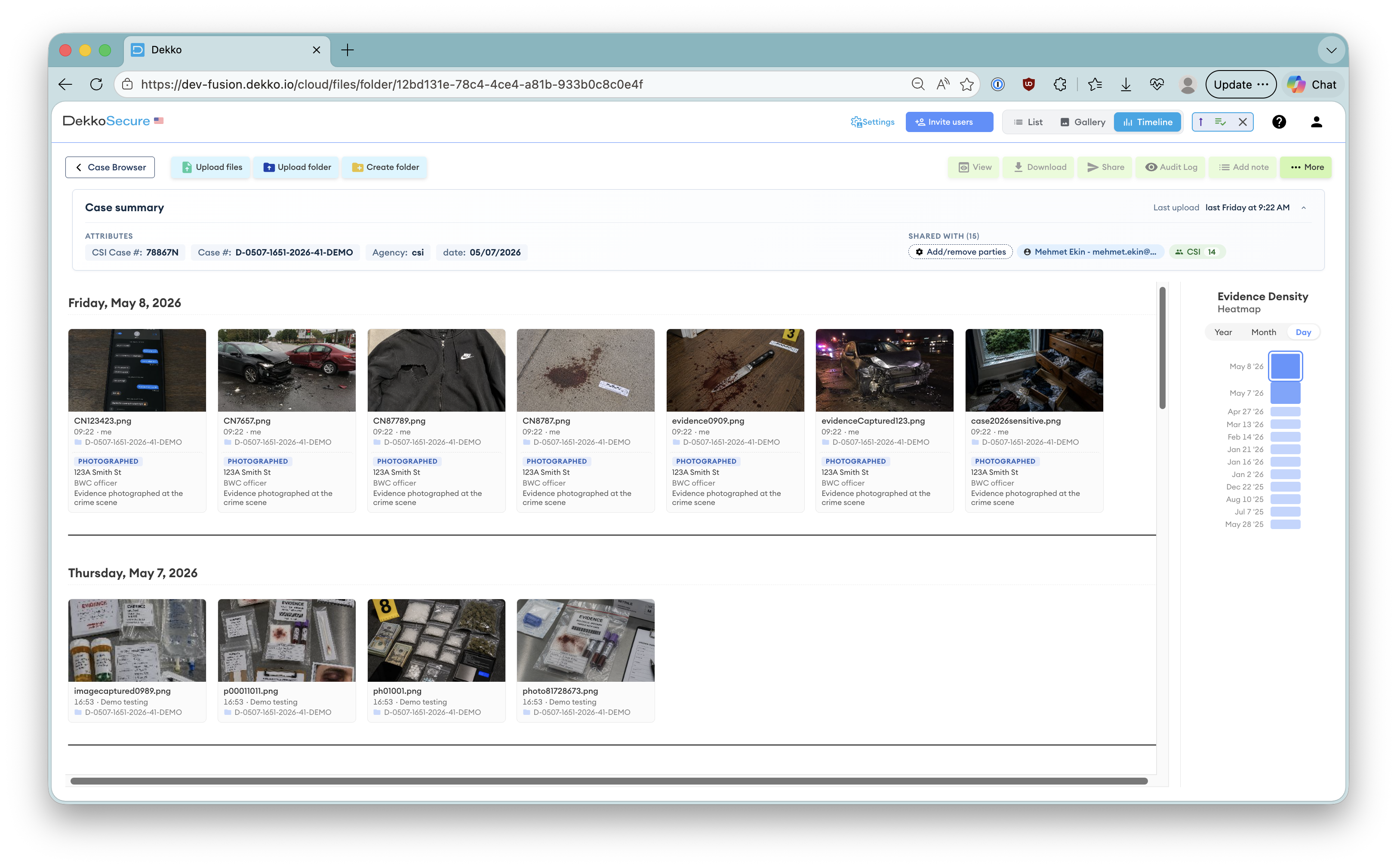
Digital evidence can be altered after transfer without detection due to the lack of a cryptographic chain of custody.
Elevated ransomware risk, with attackers able to encrypt, steal, or delete unprotected medical records from SFTP servers.
Broad access risks where personnel can download sensitive financial data without restrictions.
Inability to prove documents remain unaltered can create challenges in court proceedings.
Trade secrets stored in plaintext that competitors or insiders can access and steal.
Inter-agency file transfers without end-to-end encryption leave sensitive information exposed at rest and after delivery.
Future-Proofing File Transfer Security
Organizations that remain reliant on SFTP will face increasing risk exposure and compliance challenges. Secure file transfer will continue evolving as threats grow more sophisticated and compliance requirements become more stringent.
The future of secure file transfer is not about incremental improvements to legacy protocols. It requires a willingness to embrace fundamentally different security models built on zero-knowledge architecture and end-to-end encryption.
Whether in government, healthcare, finance, or legal, zero-knowledge security is becoming an absolute requirement for organizations handling sensitive information.
The choice is clear: continue with the incomplete security of SFTP or embrace comprehensive security models that protect your data throughout its entire lifecycle. For organizations where data security is mission-critical, only the latter offers true protection.
Common questions
Frequently Asked Questions
If SFTP already encrypts traffic, why isn't it sufficient for protecting sensitive files?
SFTP secures the transport channel, not the data itself. It verifies integrity during transit but provides no mechanism to detect changes made before upload or after download. It also relies on standard system logs that are not tamper-proof, and assumes a user remains legitimate for the entire session, exposing organizations to risks like credential theft, session hijacking, undetected data tampering, and weak forensic evidence.
What does "data-centric security" mean, and how do zero-knowledge end-to-end encryption models achieve it?
Data-centric security protects the data wherever it resides and however it moves. In a zero-knowledge, end-to-end encryption model, files and user actions are encrypted end to end so only authorized endpoints can access plaintext and the service provider never can. Encryption follows the data, ensuring confidentiality and integrity throughout its lifecycle, independent of the network path or storage location.
How do zero-trust and zero-knowledge differ, and why use both?
Zero-trust continuously verifies identity and enforces least-privilege access, never assuming any user or device is trusted by default. Zero-knowledge removes reliance on third parties by preventing even administrators from accessing plaintext data. Combined, they validate who can act and ensure that unseen parties cannot read the data, forming a security model that is mathematically verified and effectively breach-proof when properly implemented.
What do cryptographically signed audit trails provide that traditional SFTP logs do not?
Cryptographically signed audit trails are tamper-evident records that automatically capture file access, transfers, and modifications. Unlike ordinary system logs, which an attacker or compromised admin can erase or alter, signed trails provide durable, trustworthy forensic evidence and a verifiable history of every action taken.
How can we transition from SFTP to a zero-knowledge approach without disrupting operations?
Follow a phased, usability-focused plan: adopt end-to-end encryption from day one; enable cryptographically signed audit trails; integrate multi-factor authentication with single sign-on; switch to identity-based access controls; ensure the solution is intuitive so users do not seek workarounds; and migrate in phases, prioritizing the most sensitive data first to maintain continuity.