Security Insights
AES-256 Encryption for Modern Data Security
Data breaches and security failures make headlines almost daily. Agencies, healthcare providers, and law enforcement face relentless attempts to access their sensitive information. Behind the scenes of successful security systems stands a powerful guardian: AES-256 encryption.
We have spent years implementing data security solutions for teams handling the most sensitive information. Understanding encryption fundamentals is not just academic. It is essential for anyone responsible for protecting critical data.
What Exactly Is AES-256?
AES (Advanced Encryption Standard) represents the gold standard in symmetric encryption. The "256" refers to the key length in bits, making it the strongest variant available in widespread use. This mathematical algorithm transforms readable data into a scrambled format that remains indecipherable without the correct key, strengthening data security across systems.
AES replaced the outdated Data Encryption Standard (DES) following a rigorous multi-year selection process and scrutiny by the global cryptographic community. AES-256 emerged as the preferred standard for protecting classified information and remains so today.
What makes it special? Mathematics. AES-256 uses 14 rounds of complex substitutions and permutations to thoroughly scramble data.
Breaking this encryption through brute force would require trying 2256 possible keys, a number so astronomically large that even with all the computing power on Earth, it would take billions of years to crack.
Beyond the Technical Jargon
Think of encryption as a vault for your data, especially in end-to-end encryption models. The difference between weak encryption and AES-256 is like comparing a basic padlock to a sophisticated bank vault with time locks, motion sensors, and reinforced walls.
When implemented correctly, AES-256 provides:
-
Confidentiality Ensuring only authorized users can read the information.
-
Data integrity Detecting if information has been tampered with.
-
Authentication Verifying the source of encrypted communications.
These properties underpin end-to-end encryption and zero-knowledge designs used in high-assurance environments, making AES-256 ideal for protecting communications between government agencies, securing patient data in healthcare systems, and safeguarding evidence in law enforcement investigations.
Real-World Applications
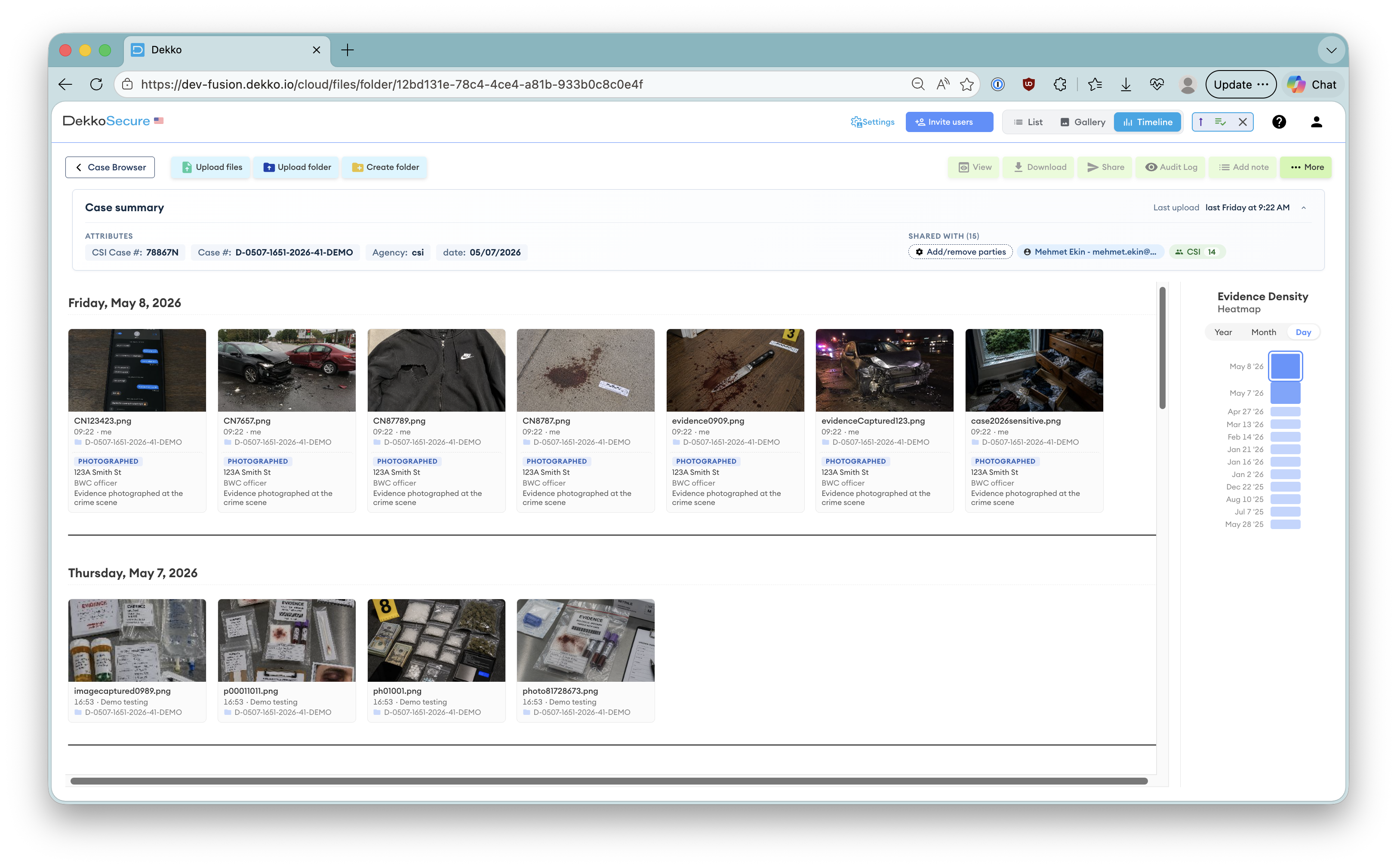
In practice, AES-256 forms the backbone of secure file-sharing platforms, encrypted communications, and data storage systems. Some platforms adopt a zero-knowledge approach so providers cannot read customer content.
When teams can share information without fear of interception or compromise, operational efficiency increases dramatically. Proper encryption transforms both an organization's security posture and its ability to collaborate on sensitive matters.
Implementation Considerations
While AES-256 itself is virtually unbreakable, security depends on proper implementation. The strongest lock is useless if you leave the key under the doormat.
Key management remains critical. Processes for generating, distributing, storing, and revoking encryption keys must be secure. The infrastructure surrounding encryption often presents more vulnerabilities than the encryption itself. Complementary zero-knowledge architectures limit who can ever access plaintext or keys.
End-to-end encryption ensures data remains protected throughout its entire journey, from creation to storage to sharing. Partial encryption solutions leave gaps that sophisticated attackers can exploit. Paired with a zero-knowledge model, end-to-end encryption further reduces insider and third-party risk.
Security Without Compromise
The strength of modern encryption systems lies in balancing security with usability. Legacy systems often force users to choose between convenience and protection, leading to dangerous workarounds and security fatigue.
Today's implementations make security accessible. Users should not need cryptography expertise to benefit from encryption. The most effective security measures work silently in the background, protecting information without disrupting workflows. Modern end-to-end encryption and zero-knowledge patterns deliver robust protection without burdening users.
As security threats evolve, AES-256 continues to stand firm. No practical attacks have succeeded against properly implemented AES-256 encryption, which is why it remains trusted for the most sensitive applications globally.
For teams handling truly sensitive information, understanding encryption fundamentals is the first step toward comprehensive data protection.
The investment in proper encryption pays dividends through risk reduction, compliance adherence, and operational peace of mind.
Common questions
Frequently Asked Questions
What exactly is AES-256, and why is it considered the gold standard in encryption?
AES-256 is the strongest widely used variant of the Advanced Encryption Standard, a symmetric encryption algorithm that replaced DES following a rigorous global selection process. With a 256-bit key and 14 rounds of mathematical substitutions and permutations, it scrambles data into a form unreadable without the correct key. It earned trust through extensive international scrutiny and is relied on to protect even classified information.
Can AES-256 be cracked in practice?
Not with today's or foreseeable computing power when implemented correctly. Brute-forcing a 256-bit key requires trying 2256 possibilities, an astronomically large number, making such attacks impractical. To date, no practical attacks have succeeded against properly implemented AES-256.
What security properties does AES-256 provide?
When correctly implemented, AES-256 supports confidentiality (only authorized users can read data), data integrity (tampering is detectable), and authentication (the source of communications can be verified). These properties underpin end-to-end encryption and zero-knowledge designs used in high-assurance environments.
Where is AES-256 used in the real world?
It powers secure file-sharing platforms, encrypted communications, and data storage systems, including end-to-end encrypted workflows. Government agencies rely on it for classified data, healthcare providers use it to protect patient records and support compliance requirements, and law enforcement uses it to preserve the chain of custody for digital evidence. Proper encryption also enables teams to collaborate more efficiently by reducing fear of interception.
If AES-256 is so strong, what are the real weak points to watch?
Implementation and key management. The surrounding infrastructure, including how keys are generated, distributed, stored, and revoked, often introduces more risk than the cipher itself. End-to-end encryption prevents exposure at any point in the data's journey, and zero-knowledge architectures limit who can ever access plaintext or keys, reducing insider and third-party risk. Modern systems aim to deliver this protection without burdening users or disrupting workflows.